Sophisticated Scam Exploits Note-Taking Application to Target Cryptocurrency Community
According to Elastic Security Labs, cybercriminals are deploying a complex, multi-stage social engineering attack targeting cryptocurrency and financial sector professionals, leveraging community plugin capabilities within a note-taking platform to distribute device-hijacking malware.

A warning has been issued to cryptocurrency users regarding a newly discovered social engineering attack that manipulates victims into installing community plugins on Obsidian, a note-taking application, resulting in the unwitting execution of malware capable of commandeering their computing devices.
In a report released Tuesday, Elastic Security Labs revealed the discovery of an innovative attack campaign directed at individuals working in cryptocurrency and financial services, utilizing "elaborate social engineering on LinkedIn and Telegram" to deceive targets into permitting malicious software, disguised as benign applications, to operate on their systems.
The threat actors exploit Obsidian's community plugin infrastructure to "silently execute code when a victim opens a shared cloud vault," with the malicious campaign proving effective against both Windows and macOS operating systems.
This represents the most recent known offensive campaign directed at cryptocurrency users, who remain prime targets for fraudsters due to the irreversible nature of blockchain-based transactions. According to Chainalysis data, individual crypto wallet compromises resulted in $713 million in losses during 2025.
According to Elastic's findings, the fraudsters initiate contact with potential victims on LinkedIn while posing as representatives of a venture capital organization, then progressively redirect the conversation to Telegram where discussions center on "financial services, specifically cryptocurrency liquidity solutions, creating a plausible business context."
The threat actors request that their intended target utilize Obsidian, presenting it as their fabricated organization's database system for gaining access to a collaborative dashboard, and the prospective victim receives credentials to establish a connection to an attacker-controlled cloud-hosted vault.
"This vault is the initial access vector," Elastic stated. "Once opened in Obsidian, the target is instructed to enable community plugins sync. After that, the trojanized plugins silently execute the attack chain."
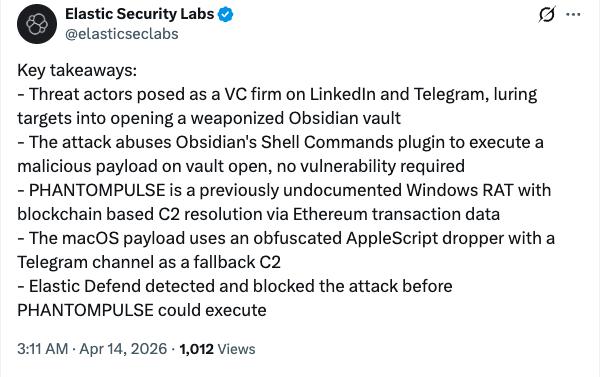
While the attack methodology varies slightly between Windows and macOS platforms, both deployment strategies install a previously undiscovered remote access trojan, or RAT, which Elastic researchers have designated "PHANTOMPULSE."
The malicious software, camouflaged as authentic applications, grants the attackers complete control over the compromised device, with Elastic noting it was "designed for stealth, resilience, and comprehensive remote access."
According to Elastic's analysis, PHANTOMPULSE employs a decentralized command-and-control infrastructure through no fewer than three distinct blockchain networks, utilizing on-chain transaction information associated with a particular wallet to establish communication with the attacker and obtain operational instructions.
"This technique provides the operator with an infrastructure-agnostic rotation capability," Elastic explained. "Because blockchain transactions are immutable and publicly accessible, the malware can always locate its C2 [command-and-control mechanism] without relying on centralized infrastructure."
"The use of three independent chains adds redundancy: even if one chain's explorer is blocked or unavailable, the remaining two provide alternative resolution paths," the research team elaborated.
While Elastic reported successfully blocking the attack campaign, the incident demonstrates that threat actors "continue to find creative initial access vectors" since exploiting Obsidian's community-managed plugin environment enabled them to circumvent "traditional security controls entirely, relying on the application's intended functionality to execute arbitrary code."
The security firm emphasized that financial institutions and cryptocurrency organizations "should be aware that legitimate productivity tools can be turned into attack vectors," and that businesses should implement app-level plugin policies as a defensive measure against comparable attacks.
