Legal Expert Claims Drift Protocol Breach Could Constitute 'Civil Negligence'
North Korea-linked threat actors are believed to be responsible for the Drift Protocol exploit that resulted in $280 million in losses.
Attorney Ariel Givner has stated that the exploitation of Drift Protocol, a Solana-based decentralized finance (DeFi) platform, could potentially be classified as "civil negligence," as the breach might have been avoided had the Drift team adhered to standard operational security protocols.
"In simple language, civil negligence indicates they didn't fulfill their fundamental obligation to safeguard the funds under their management," Givner explained in her response to the post-mortem analysis shared by the Drift team regarding their handling of the $280 million exploit that occurred on Wednesday.
According to Givner, the Drift team neglected to implement "fundamental" security measures, such as maintaining signing keys on isolated, "air-gapped" systems that remain completely separate from developer workstations, and performing thorough background checks on blockchain developers encountered at industry conferences.
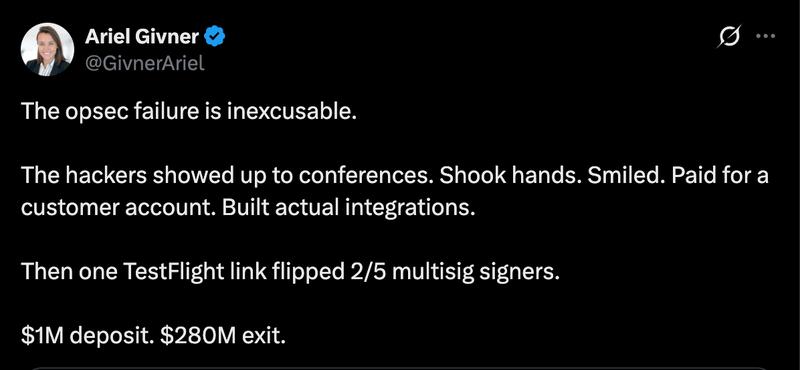
"All reputable projects understand this requirement. Drift failed to implement it," she stated, further noting, "They were aware that the crypto space is rife with hackers, particularly North Korean state-sponsored teams." Givner elaborated:
"Nevertheless, their team dedicated months to communicating on Telegram, encountering unknown individuals at conferences, accessing questionable code repositories, and installing suspicious applications on devices connected to multisignature controls."
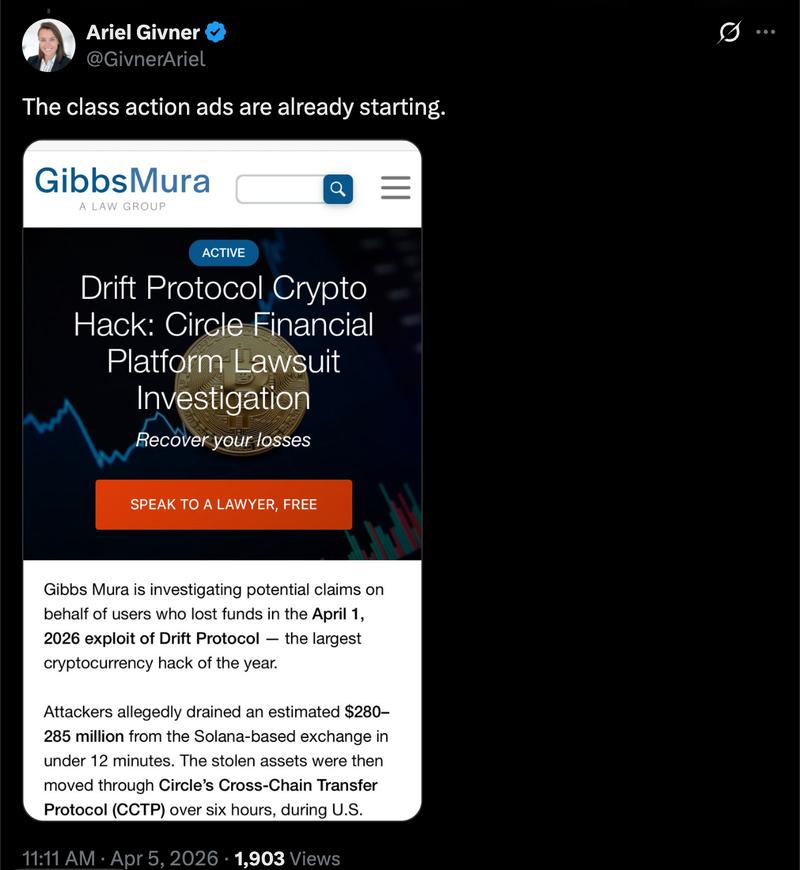
This breach serves as a stark warning that social engineering tactics and infiltration of projects by threat actors represent significant attack vectors targeting cryptocurrency developers, with the potential to deplete user funds and cause irreparable damage to customer confidence in affected platforms.
Drift Protocol says attack took "months" of planning
On Saturday, the Drift Protocol team released an update detailing the mechanics of the exploit and asserted that the attackers spent six months meticulously planning the attack before carrying it out.
The threat actors initially made contact with the Drift team at a "major" cryptocurrency industry conference in October 2025, presenting themselves as parties interested in protocol integrations and potential collaboration opportunities.
Over the following six months, the malicious actors systematically cultivated relationships with the Drift development team, and after establishing sufficient trust, they proceeded to distribute malicious links and deploy malware that successfully infiltrated developer machines.
The Drift team noted that these individuals, who are believed to be working on behalf of North Korea state-affiliated hacking groups and who made physical contact with Drift developers, were not themselves North Korean nationals.
With "medium-high confidence," Drift stated that the exploit was executed by the identical actors responsible for the Radiant Capital hack in October 2024.
Radiant Capital disclosed in December 2024 that their exploit was perpetrated through malware transmitted via Telegram by a North Korea-aligned hacker who had disguised themselves as a former contractor.
