Succinct Unveils Zcam iPhone Application for Cryptographic Photo Authentication
Succinct, a company specializing in cryptography, has introduced Zcam, a camera application for iPhone that cryptographically signs images and videos during capture to verify media authenticity amid growing AI concerns.

A cryptography-focused firm called Succinct has introduced Zcam, a camera application designed for iPhone devices that applies cryptographic signatures to photographs and videos in real-time as they are captured, providing a mechanism to validate their genuineness.
In an announcement made on Thursday, the company explained that Zcam integrates a tamper-resistant record that creates a connection between digital media and the specific device used to capture it, enabling anyone viewing the content to confirm it hasn't been digitally modified or created using artificial intelligence technologies.
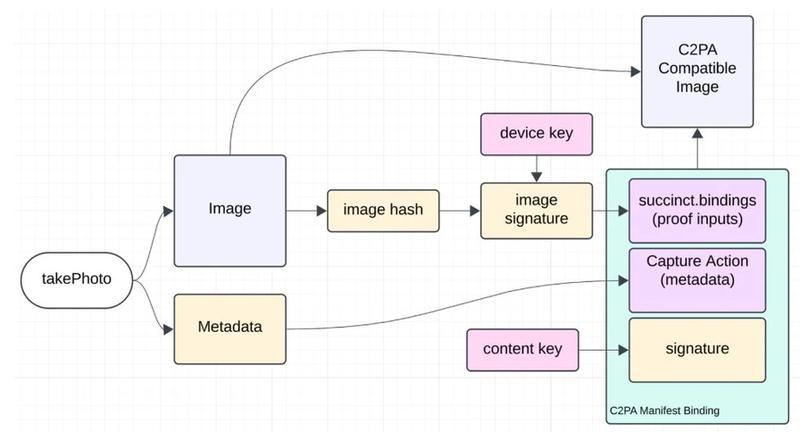
Based on information provided by Succinct, the application functions through a process that involves hashing unprocessed image data and applying a digital signature using cryptographic keys that are created within Apple's Secure Enclave, which is a hardware-based security component. The signature that results from this process, together with metadata from the capture and attestation information, gets embedded directly into the media file utilizing the Coalition for Content Provenance and Authenticity (C2PA) standard, which represents a framework designed for attaching tamper-resistant provenance information to digital media files.
The C2PA and similar standards are built to verify the origin and modification history of digital content through the embedding of signed provenance metadata within files. As stated by the C2PA organization, this open technical standard enables publishers, content creators and consumers to determine the "origin and edits" of any piece of digital content. The standard provides users with the capability to document the content creation process, identify which tools and technologies were employed and track how the content has been modified throughout its lifecycle.
This product launch represents Succinct's expansion of its applied cryptography expertise from the realm of blockchain infrastructure into the domain of media provenance, reflecting a broader industry trend where organizations are seeking methods to authenticate digital content at the point of creation instead of depending solely on AI detection tools that operate after content has already been produced.
The timing of this launch coincides with an expanding landscape of security concerns within the cryptocurrency sector that increasingly involve AI-powered fraudulent activities. In a separate announcement on Thursday, CertiK, a blockchain security company, issued a warning stating that deepfakes, phishing campaigns and social engineering attacks enhanced by AI are expected to be responsible for some of the most significant crypto security breaches in 2026. Their report emphasized the ways in which malicious actors are leveraging highly convincing synthetic media to manipulate users and circumvent existing security measures.
Crypto security expands beyond code as AI threats rise
According to Succinct's statement, Zcam represents an initial milestone in the direction of wider acceptance and implementation of cryptographic provenance technologies, which have potential applications in numerous fields including journalism, processing of insurance claims and identity verification systems, where maintaining trust in the authenticity of digital media has become increasingly vital.
The company also provided transparent disclosure about certain limitations present in the current version of their implementation, pointing out that the Zcam software development kit has not undergone a security audit and should not be considered ready for production deployment. Additionally, Succinct acknowledged that secure enclaves have experienced security compromises in previous instances and that achieving a completely tamper-proof process from capture through signing continues to be an ongoing area of research and development.
