Quantum Computing Challenges: How Bitcoin and Ethereum Chart Divergent Paths
While both Bitcoin and Ethereum confront identical quantum computing risks, their mitigation strategies differ substantially. Discover how these contrasting approaches illuminate fundamental distinctions in design philosophy and network governance.

Understanding the quantum divergence in Bitcoin and Ethereum
For years, quantum computing has been perceived as a far-off, predominantly academic concern for blockchain infrastructure. That perception, however, is beginning to shift.
As leading tech giants like Google unveil roadmaps for implementing post-quantum cryptographic solutions, and as cryptocurrency experts revisit previously accepted security models, the conversation is transitioning from theoretical discussions to actionable strategies.
Yet Bitcoin and Ethereum, the two dominant blockchain platforms, are tackling the quantum computing challenge through distinctly different methods. While both systems utilize cryptographic frameworks that could theoretically be undermined by sufficiently advanced quantum machines, their respective strategies for mitigating this common vulnerability are developing along notably divergent trajectories.
This separation, frequently described as the "quantum gap," relates less to cryptographic mathematics and more to how each platform manages evolution, consensus-building and forward-looking security measures.
Did you know? Quantum computers do not need to break every wallet at once. They only need access to exposed public keys, which means older Bitcoin addresses that have already transacted could theoretically be more vulnerable than unused ones.
The significance of quantum computing for blockchain networks
Blockchain platforms depend extensively on public-key cryptography, especially elliptic curve cryptography (ECC). This system enables users to generate a public address from a private key, facilitating secure value transfers while maintaining the confidentiality of sensitive data.
Should quantum computers reach adequate scale and sophistication, they could seriously undermine this cryptographic foundation. Computational methods like Shor's algorithm could potentially enable quantum machines to derive private keys straight from public keys, thus threatening wallet security and the integrity of transaction validation.
The prevailing view among experts is that quantum computers powerful enough to threaten current cryptography remain years, possibly decades, from realization. However, blockchain networks face a unique predicament. They cannot be upgraded overnight. Any significant transition demands extensive planning, comprehensive testing and widespread community acceptance spanning multiple years.
This creates an important contradiction: While the danger is not imminent, preparatory measures must commence considerably in advance.
Outside forces are intensifying the conversation
The dialogue has expanded far beyond cryptocurrency-focused circles. In March 2026, Google revealed a target timeline to migrate its infrastructure to post-quantum cryptography by 2029. The company emphasized that quantum computers represent a substantial threat to current encryption methods and digital signature systems.
This announcement carries particular weight for blockchain infrastructure because digital signatures are central to confirming ownership. While encryption faces vulnerability through "store-now, decrypt-later" attack vectors, digital signatures confront a different danger. If they are compromised, the risk of unauthorized fund transfers could escalate significantly.
As prominent organizations start implementing quantum-resistant strategies, blockchain platforms encounter increasing expectations to articulate their own defensive measures. This is precisely where the contrasts between Bitcoin and Ethereum emerge most clearly.
Did you know? The term "post-quantum cryptography" does not refer to quantum technology itself. It refers to classical algorithms designed to resist quantum attacks, allowing existing computers to defend against future quantum capabilities without requiring quantum hardware.
Bitcoin's strategy: Cautious and gradual
Bitcoin's response to quantum vulnerability is shaped by its foundational principles: limit alterations, preserve consistency and prevent introducing needless complexity to the core protocol.
Among the most prominent proposals addressing this concern is Bitcoin Improvement Proposal 360 (BIP-360), which presents the Pay-to-Merkle-Root (P2MR) concept. Rather than comprehensively transforming Bitcoin's underlying cryptographic architecture, this proposal aims to reduce vulnerability by modifying how certain transaction outputs are structured.
The intention is not to implement complete quantum protection for Bitcoin through a single update. Instead, it seeks to establish a framework for introducing more secure transaction formats while maintaining compatibility with the current network infrastructure.
This methodology reflects the prevailing attitude throughout the Bitcoin ecosystem. Community deliberations typically involve extended planning horizons, spanning anywhere from five years to multiple decades. The emphasis centers on guaranteeing that modifications do not compromise Bitcoin's foundational values: decentralization and consistency.
However, this conservative stance has faced pushback. Critics suggest that postponing more thorough protective measures might leave the network exposed if quantum breakthroughs materialize sooner than anticipated. Meanwhile, others maintain that implementing rushed modifications could create unnecessary vulnerabilities in a system engineered for enduring stability.
Ethereum's strategy: Systematic and flexible
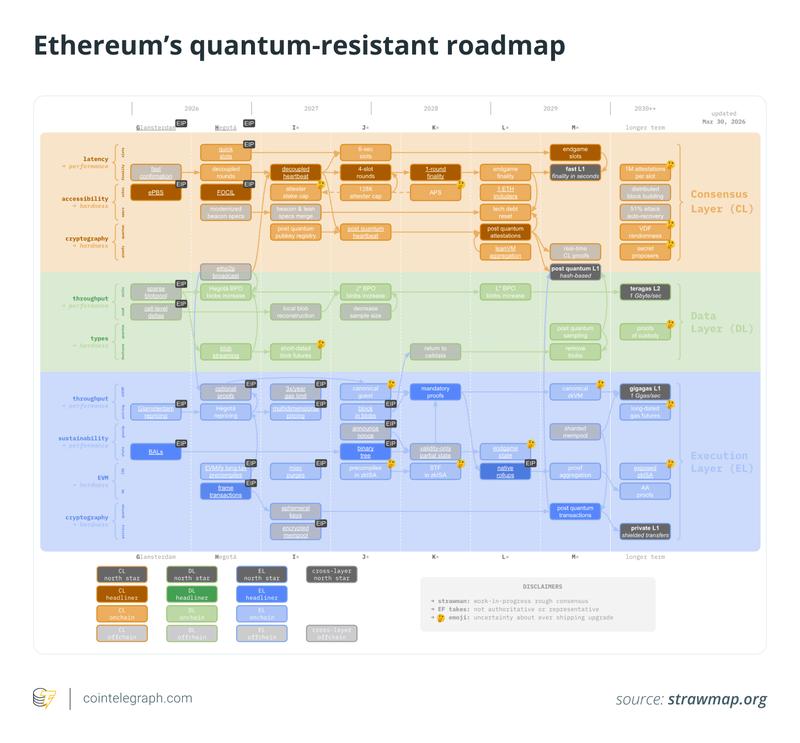
Ethereum, conversely, is implementing a more forward-looking and organized approach. The Ethereum development community has started establishing a post-quantum roadmap that frames the issue as a comprehensive system-wide enhancement rather than an isolated technical modification.
A central component of Ethereum's methodology is "cryptographic agility," meaning the capacity to swap fundamental cryptographic building blocks without compromising network integrity. This philosophy harmonizes with Ethereum's overall design ethos, which prioritizes adaptability and ongoing progressive refinement.
The roadmap addresses several layers:
- Execution layer: Investigating account abstraction and alternative signature schemes that can support post-quantum cryptography.
- Consensus layer: Assessing replacements for validator signature mechanisms, including hash-based options.
- Data layer: Modifying data availability structures to ensure security in a post-quantum setting.
Ethereum developers have designated post-quantum security as a critical long-term objective, with implementation timelines reaching toward the decade's conclusion.
Unlike Bitcoin's step-by-step proposals, Ethereum's methodology resembles a phased transition blueprint. The objective is not rapid deployment but systematic preparation, positioning the network to adapt when the danger becomes more tangible.
What drives Bitcoin and Ethereum toward different quantum threat strategies
The contrasting methodologies adopted by Bitcoin and Ethereum are not random occurrences. They stem from core differences in system design, decision-making processes and philosophical foundations.
Bitcoin's protocol layer is engineered for durability and consistency, which promotes a conservative posture regarding substantial protocol modifications. Any proposed change must satisfy rigorous consensus thresholds and, even after approval, typically remains constrained in scope.
Ethereum, alternatively, possesses an established history of synchronized upgrades and protocol transformation. From transitioning to proof-of-stake through continued scalability enhancements, the platform has shown readiness to implement sophisticated changes when circumstances demand.
This fundamental difference influences how each network interprets the quantum challenge. Bitcoin typically perceives it as a distant possibility warranting deliberate, limited action. Ethereum approaches it as a network-wide concern requiring advance planning and structural flexibility.
From this perspective, the "quantum gap" represents less of a disagreement about threat severity and more about how each community defines prudent preparation.
Did you know? Some early Bitcoin transactions reused addresses multiple times, unintentionally increasing their exposure. Modern wallet practices discourage address reuse partly because of long-term risks such as quantum attacks, even though the threat is not immediate.
Both Bitcoin and Ethereum face unresolved quantum challenges
Notwithstanding their contrasting approaches, neither Bitcoin nor Ethereum has completely addressed the quantum computing threat.
Bitcoin is actively exploring multiple proposals and evaluating compromises, yet no definitive transition strategy has received formal acceptance. Ethereum, while further along in its preparation, still confronts significant technical obstacles and coordination requirements before its roadmap achieves full implementation.
Multiple critical questions affect both platforms:
- How to migrate existing assets protected by vulnerable cryptography
- How to coordinate upgrades within decentralized communities
- How to balance backward compatibility and forward security
These challenges emphasize the multifaceted nature of the problem. Post-quantum security extends beyond a mere technical enhancement. It also serves as an evaluation of sustained adaptability, governance structures and collective coordination.
Might security preparedness affect market perception?
As institutional awareness of quantum vulnerability intensifies, variations in readiness could ultimately influence how markets evaluate blockchain platforms.
The logic is straightforward: A platform that exhibits stronger adaptability to emerging threats may be perceived as more durable across extended timeframes.
That said, this notion remains primarily theoretical. Given that quantum dangers are still regarded as distant concerns, any immediate market impacts are more likely driven by perception rather than actual technical progress.
Nonetheless, the fact that this topic is now appearing in institutional analysis and wider public dialogue indicates that it may evolve into a more significant evaluation criterion going forward.
