$176M Bitcoin Heist: When Physical Surveillance Compromised Digital Security
A $176 million Bitcoin heist involving a compromised seed phrase reveals critical vulnerabilities in hardware wallet security that have nothing to do with hacking or malware.

Human factors trump technical vulnerabilities in cryptocurrency security breaches
Within the cryptocurrency ecosystem, protection measures are typically viewed through a technological lens. Users are instructed to protect their private keys, utilize hardware wallets and avoid suspicious links. However, a high-profile legal battle unfolding in the United Kingdom demonstrates that the greatest weakness in this particular incident may have been entirely unrelated to technology.
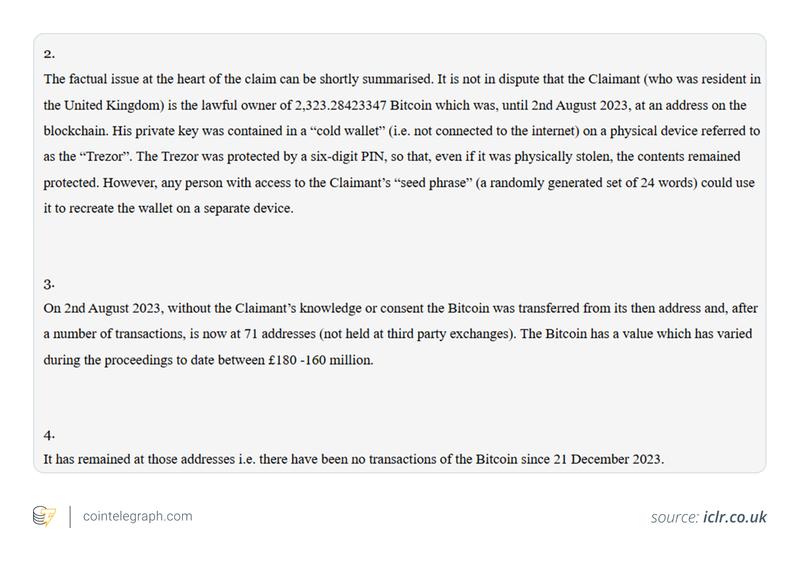
A legal proceeding currently underway at the UK High Court concerns the purported theft of 2,323 Bitcoin (BTC), valued at approximately $176 million. The alleged theft was not the result of sophisticated hacking techniques or malicious software. Rather, it originated with the exposure of a seed phrase, which became the solitary point of vulnerability in the self-custody arrangement.
The legal conflict involves Ping Fai Yuen, who alleges that Fun Yung Li, his estranged spouse, along with her sibling, obtained unauthorized access to his Bitcoin holdings by covertly capturing his wallet's recovery credentials.
The cryptocurrency was stored using a hardware wallet, a device specifically engineered to maintain private keys in an offline state and protected from remote attacks. Despite these precautions, the theft occurred and required no compromise of cryptographic security.
Legal filings indicate the theft necessitated only the acquisition of the seed phrase.
Purported sequence of events in the cryptocurrency heist
The accusations paint a picture of physical monitoring rather than electronic infiltration.
The accused parties are alleged to have employed photographic or recording equipment to obtain the seed phrase and associated security codes.
The plaintiff discovered the alleged conspiracy after being alerted by his daughter.
He subsequently installed audio surveillance equipment, which allegedly recorded discussions concerning the transfer of the cryptocurrency.
The Bitcoin holdings were then dispersed to 71 distinct wallet addresses.
No further transactions have been recorded on the blockchain following Dec. 21, 2023, suggesting that the cryptocurrency has remained dormant since the alleged transfer occurred.
Law enforcement officials are reported to have seized electronic devices and cold storage wallets during their investigation, though legal proceedings continue.
Did you know? In numerous previous incidents, concealed recording devices, rather than cybercriminals, have proven to be the critical security failure in cryptocurrency protection. Physical monitoring has silently emerged as one of the most overlooked dangers to self-managed digital holdings.
The critical role of the seed phrase in the UK cryptocurrency theft
Comprehending this case requires understanding a fundamental concept of cryptocurrency: Anyone possessing the seed phrase maintains complete authority over the associated funds.
A hardware wallet protects private keys from internet-based threats. However, the seed phrase, usually consisting of 12 to 24 words, functions as a complete restoration key for the entire wallet.
Obtaining the seed phrase enables anyone to:
Recreate the wallet on any alternative device
Gain access to all the connected cryptocurrency
Transfer the holdings without requiring the original hardware
In essence, after the seed phrase is compromised, the physical wallet becomes entirely irrelevant.
Physical monitoring: A rarely discussed security vulnerability
What makes this case particularly noteworthy is the alleged technique employed to execute the compromise.
Instead of using phishing schemes or harmful programs, the allegations focus on visual or auditory interception, potentially through concealed cameras or secret recording equipment.
This highlights a frequently overlooked danger: side-channel vulnerability.
Seed phrases are commonly documented in writing, verbalized or entered during initial configuration. When any of these actions are observed or recorded:
The complete phrase can be reconstructed.
The wallet can be duplicated on different hardware.
Cryptocurrency can be moved without leaving immediate evidence.
In settings filled with internet-connected devices, surveillance equipment and communal areas, this category of threat is increasingly prevalent.
Initial assessment by the UK High Court
The case was brought before the UK High Court, where Justice Cotter reviewed the submitted evidence.
While this represents a preliminary assessment rather than a conclusive ruling, the judge noted that the plaintiff had established an extremely strong likelihood of prevailing.
Factors taken into account included:
A prior warning about the alleged scheme
Recorded conversations
Electronic devices allegedly capable of accessing wallet data
The court additionally emphasized the urgency of the situation, referencing security risks and Bitcoin's volatile market value.
Did you know? Certain wallet solutions now incorporate decoy wallet functionality that responds to alternative PINs. This capability enables users to reveal a minimal balance when threatened, providing an additional safeguard against both physical intimidation and monitoring-based intrusions.
Strategic reasoning behind distributing assets to 71 addresses
According to the legal claim, the Bitcoin was divided among 71 separate wallet addresses.
This action has multiple ramifications:
It complicates monitoring and asset retrieval efforts.
It prevents a single substantial transaction from attracting immediate notice.
It divides the cryptocurrency, potentially postponing legal action and investigative procedures.
While blockchain transparency enables transaction monitoring, dispersing funds introduces additional complexity and extends the timeline for any retrieval attempts.
Potential dusting attack implications
The plaintiff additionally raised concerns regarding a potential dusting attack targeting the addresses in question.
Dusting involves transmitting minuscule cryptocurrency quantities to wallets for the purpose of:
Tracking future transactions
Connecting addresses to actual individuals
Discovering high-value targets for subsequent attacks
When wallet addresses are disclosed publicly, they may attract unwanted attention, regardless of whether additional transactions take place.
Broader implications beyond personal litigation
While this case represents a personal legal matter on one level, it simultaneously functions as an educational example of wider cryptocurrency custody vulnerabilities.
It illustrates that:
Hardware wallets mitigate online risks, but cannot address human-related vulnerabilities.
Dangers from individuals in close proximity may exceed those from external hackers.
Compromise of the seed phrase can lead to total loss of asset control.
Most importantly, this case establishes that cryptocurrency protection encompasses much more than technological solutions; it depends significantly on physical surroundings, behavior patterns, interpersonal trust and personal relationships.
Critical security principles derived from this case
This situation underscores several fundamental security practices:
Maintain complete isolation of seed phrases from cameras, mobile devices and internet-connected equipment.
Never store recovery credentials in locations accessible to others.
Implement separation between personal identity and wallet authority wherever feasible.
Deploy multiple security layers for substantial cryptocurrency holdings.
More advanced security configurations may incorporate supplementary passphrases, distributed backup systems or multisignature wallets. All of these approaches aim to minimize dependence on any single point of failure.
