Maryland Man Charged in $54M Uranium Finance Crypto Heist, Risks Three Decades Behind Bars
Federal prosecutors have revealed charges against a Maryland resident connected to the theft of more than $54 million from Uranium Finance during 2021, an attack that ultimately forced the cryptocurrency platform to cease operations.

Federal prosecutors have made public charges against an individual allegedly responsible for hacking Uranium Finance, a defunct decentralized finance platform that experienced losses exceeding $54 million through a pair of security breaches during 2021.
On Monday, the US Attorney's Office for the Southern District of New York brought charges against Jonathan Spalletta, a Maryland resident, for allegedly executing two distinct cyberattacks on Uranium Finance in April 2021. Spalletta turned himself in to law enforcement on the same day.
According to a statement released by US Attorney Jay Clayton, Spalletta manipulated smart contract vulnerabilities to siphon millions in digital assets from Uranium Finance, ultimately forcing the platform to cease operations when it ran out of available funds.
Stealing from a crypto exchange is stealing—the claim that 'crypto is different' does not change that. For the victims, there is nothing different about having your money taken. Spalletta cost real victims real losses of tens of millions of dollars, and now he's under real arrest.
Uranium Finance operated as a BNB Chain-based fork of the automated market maker Uniswap, launching operations in April 2021 amid the cryptocurrency bull run. The platform's website went dark following the second security breach, leaving affected users with minimal information or recourse ever since.

Two hacks in the same month killed the exchange
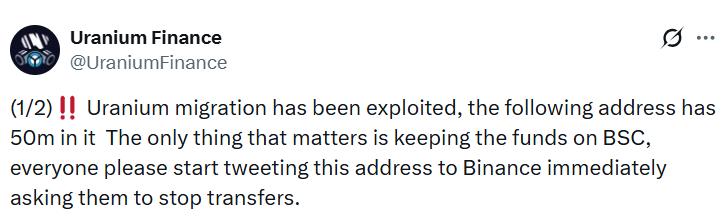
The first security breach hit Uranium Finance on April 8, 2021, mere days following its initial launch, when a malicious actor took advantage of a smart contract vulnerability to "withdraw far more rewards in cryptocurrency" than their authorized allocation, based on information from the US Attorney's Office of the Southern District of New York.
The platform subsequently negotiated a private settlement with the attacker, which led to the reimbursement of all stolen assets except for $386,000.
During a more devastating second attack several weeks afterward, on April 28, a malicious party exploited a flaw in the Uranium smart contract that controlled withdrawal restrictions across 26 different liquidity pools to abscond with $53.3 million worth of cryptocurrency, comprising Bitcoin (BTC), Ether (ETH) and "U92" tokens, which served as the platform's native digital currency.
Funds allegedly spent on Pokémon cards, Roman coins
According to prosecutors, the embezzled cryptocurrency was converted into purchases of collectible items, such as Pokémon trading cards, ancient Roman currency pieces and a fragment of fabric from the Wright brothers' historic aircraft. Law enforcement confiscated these items when they conducted a search of Spalletta's home.
During February of the previous year, law enforcement officials confiscated $31 million worth of cryptocurrency connected to the security breach but provided no additional information at that time.
Spalletta faces one count of computer fraud, which carries a maximum penalty of up to 10 years imprisonment, and one count of money laundering, which carries a maximum penalty of up to 20 years behind bars.
His initial court appearance was scheduled for Monday before US Magistrate Ona Wang to officially receive notification of the charges against him.
According to industry estimates, malicious actors successfully stole in excess of $2.6 billion via hacks and security exploits throughout 2021, with the most significant incident being a $610 million assault on Poly Network, a cross-chain DeFi protocol. That particular hacker subsequently returned the stolen assets, with the development team characterizing the incident as a white-hat operation.