Google Reveals Quantum Computers May Break Cryptocurrency Encryption With Fewer Qubits Than Expected
The tech giant has revised its calculations regarding the quantum computing power necessary to compromise elliptic curve cryptographic systems.

Recent findings from Google indicate that the computational power required by quantum computers to compromise the cryptographic security protecting cryptocurrency networks may be significantly lower than earlier projections suggested.
According to Google's latest research, published this Monday, quantum computing systems might be capable of breaking the encryption safeguarding Bitcoin (BTC) and Ethereum (ETH) with less than 500,000 physical qubits, considering present assumptions regarding hardware performance. The fundamental computational unit of quantum computing is known as a qubit.
The research team developed two distinct quantum circuits for evaluation on a superconducting-qubit, cryptographically relevant quantum computer (CRQC), documenting that this represented a "20-fold reduction" in the qubit count necessary to solve the 256-bit elliptic curve discrete logarithm problem (ECDLP-256) that cryptocurrency networks commonly employ.
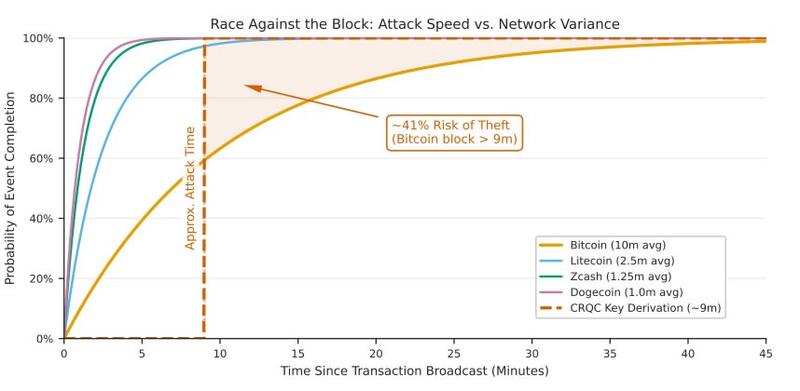
According to the findings, in a hypothetical situation, a quantum computing system might be able to break a Bitcoin private key in approximately nine minutes, creating a narrow opportunity to execute an "on-spend attack" considering Bitcoin's 10-minute block time interval.
An "on-spend" quantum attack represents a theoretical future scenario in which a quantum computer successfully determines a private key by analyzing a public key that becomes visible during a transaction, enabling the attacker to redirect the funds.
"We should estimate the time required to launch an on-spend attack starting from this primed state at the moment the public key is learned to be roughly either 9 minutes or 12 minutes."
"My confidence in Q-Day by 2032 has shot up significantly. IMO there's at least a 10% chance that by 2032 a quantum computer recovers [...] private key from an exposed public key," said co-author and Ethereum researcher Justin Drake.
Ethereum is vulnerable to "at-rest attacks"
The research team additionally cautioned that Ethereum's account structure is "structurally prone to at-rest attacks," indicating these attacks don't depend on specific timing constraints.
An "at-rest" attack operates similarly by leveraging a public key to calculate a private key through quantum computing, however, in this instance, there's no requirement to accomplish this within a limited time frame.
Once an Ethereum account broadcasts its initial transaction, its public key becomes permanently exposed on the blockchain ledger. An attacker using quantum computing can work at their own pace to calculate the private key from any publicly visible key.
"This results in account vulnerability: a systemic, unavoidable exposure that cannot be mitigated by user behavior, short of a protocol-wide transition to PQC [post-quantum cryptography]," it stated.
Google calculated that the top 1,000 wealthiest Ethereum accounts with exposed keys, containing approximately 20.5 million ETH, might be compromised in under nine days.
The technology company stated its intention to increase awareness regarding this vulnerability and is "providing the cryptocurrency community with recommendations to improve security and stability before this is possible."
Google advocated for blockchain networks to adopt PQC immediately instead of delaying until actual threats materialize.
Quantum deadline accelerated
This Wednesday, Google established a 2029 target date for its post-quantum cryptography transition, cautioning that "quantum frontiers" could be closer than they appear.
One day later, crypto entrepreneur Nic Carter said elliptic curve cryptography is on the "brink of obsolescence," adding that Ethereum developers were already working on solutions while Bitcoin developers had a "worst in class approach."
The Ethereum Foundation released its post-quantum roadmap in February, while co-founder Vitalik Buterin said validator signatures, data storage, accounts and proofs must change to prepare for quantum threats.