CertiK Report: North Korea Has Transformed Cryptocurrency Theft Into Industrial-Scale Operation
Hackers with ties to North Korea were responsible for approximately $2.06 billion out of $3.4 billion in cryptocurrency stolen through hacks during 2025, with their methods evolving from phishing attacks to physical infiltration tactics, according to CertiK's latest findings.

According to CertiK, hackers with connections to North Korea were responsible for stealing approximately 60% of the total value lost through cryptocurrency hacks during 2025, with the stolen funds being utilized to support the regime's nuclear weapons and ballistic missile development programs, underscoring the nation's increasing dependence on digital currencies as a source of hard currency generation.
These revelations, provided to Cointelegraph on Tuesday, originate from a recently released Skynet report that links approximately $2.06 billion out of a total estimated $3.4 billion in cryptocurrency security breaches during 2025 to entities associated with the Democratic People's Republic of Korea, or DPRK, representing 79 incidents out of 656 documented cases throughout that year.
From 2016 through the beginning of 2026, actors linked to the DPRK successfully stole an estimated total of $6.75 billion in digital currencies across 263 documented security incidents, according to the report, which references research conducted by independent onchain investigator Taylor Monahan.
The analysis conducted by CertiK determines that North Korea has successfully "industrialized" the theft of cryptocurrency, transforming it into a fundamental state revenue generation mechanism, with publicly available estimates demonstrating how these criminal operations account for a significant portion of the regime's foreign income, as the theft of digital assets has evolved into a reliable revenue stream for the nation.
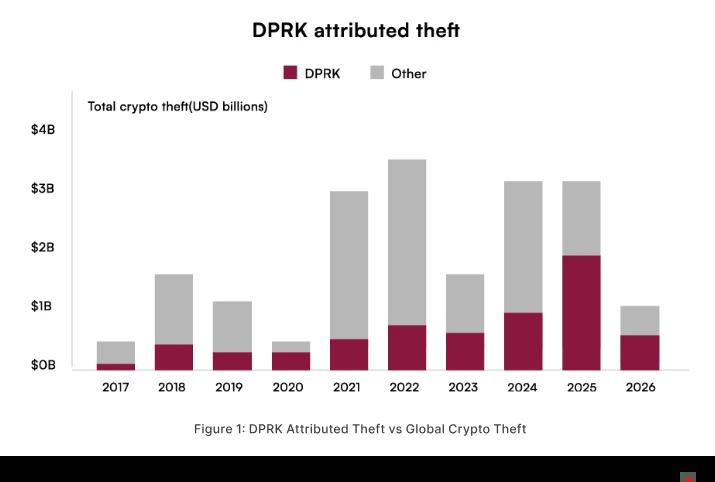
The report additionally identifies a strategic transformation from opportunistic compromises targeting hot wallets toward a smaller number of higher-value operations that specifically focus on the largest concentrations of capital.
During 2025, groups with DPRK connections were responsible for approximately 60% of the total value that was stolen while accounting for only roughly 12% of the total number of incidents, underscoring what CertiK characterizes as an emphasis on "precision and scale."
The most significant single incident, the Bybit exploitation that occurred in February 2025, led to approximately $1.5 billion in losses and is linked in the report to the TraderTraitor cluster through a supply chain attack compromising a third-party signing service provider.
In this particular case, onchain analysis performed by CertiK revealed that approximately 86% of the stolen Ether was transformed into Bitcoin within a one-month period following the hack, utilizing mixing services, bridges enabling cross-chain transfers, decentralized exchanges and over-the-counter trading brokers.
North Korea's crypto hacks shift from phishing to physical
The Skynet study from CertiK also outlines a progression in attack methodologies, demonstrating that social engineering continues to be the predominant initial attack vector, encompassing fraudulent job opportunities, impersonation of investors and malicious code repositories.
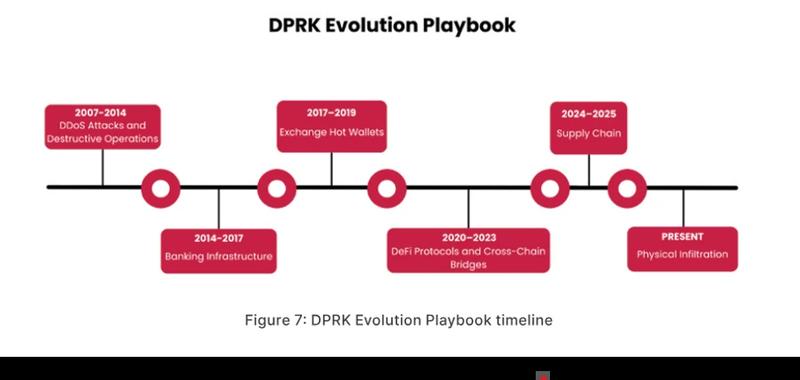
The report connects the Ronin Bridge exploitation in 2022 to a spearphishing operation that involved a fraudulent LinkedIn recruiter and a PDF document embedded with malware, whereas Bybit is referenced as a case study of supply chain compromise, in which attackers successfully manipulated a user interface to redirect funds toward a malicious address while maintaining the appearance of legitimate transaction content.
The most current evolution in tactics, which CertiK describes as "physical infiltration," is exemplified by the April 2026 Drift Protocol incident, during which approximately $285 million was extracted from a Solana-based platform following a six-month long operation that involved attending industry conferences, cultivating professional relationships and manipulating governance mechanisms.
Jonathan Riss, blockchain intelligence analyst at CertiK, informed Cointelegraph that operations linked to the DPRK currently combine intelligence agency tradecraft with sophisticated technical exploits, issuing a warning that North Korean information technology workers and intermediaries are capable of securing trusted positions within Western cryptocurrency and fintech companies by operating under fabricated identities.
The CertiK report, referencing United Nations monitoring bodies and United States intelligence agency assessments, indicates that revenue generated from these cryptocurrency thefts has been confirmed to provide support for North Korea's nuclear weapons and ballistic missile development programs, transforming the issue from merely a cybersecurity threat into one affecting international security, based on those referenced assessments.