How an Old 2017 Linux Vulnerability Has Become a Critical Threat to Cryptocurrency
A Linux security flaw known as 'Copy Fail' poses significant risks to cryptocurrency platforms running on Linux-based systems, underscoring escalating cybersecurity challenges facing the digital currency sector.

1. Copy Fail: A Linux security weakness threatening crypto platform stability
Cybersecurity professionals, governmental organizations and the digital currency industry are raising alarms about a newly discovered security weakness in Linux systems. Known by its codename "Copy Fail," this vulnerability has been present in numerous widely-used Linux distributions that have been deployed since 2017.
When certain conditions are met, this security gap could enable malicious actors to elevate their system permissions and obtain complete root-level access to compromised systems. The Cybersecurity and Infrastructure Security Agency (CISA) has incorporated this vulnerability into its Known Exploited Vulnerabilities catalog, underscoring the critical danger it represents to enterprises across the globe.
For cryptocurrency businesses and platforms, this represents far more than just another routine software vulnerability. The majority of critical infrastructure supporting exchanges, blockchain validation systems, digital asset custody platforms and node operations runs on Linux. Consequently, a vulnerability embedded at the operating system level has the potential to trigger widespread disruptions throughout substantial portions of the digital currency ecosystem.
2. What is "Copy Fail"?
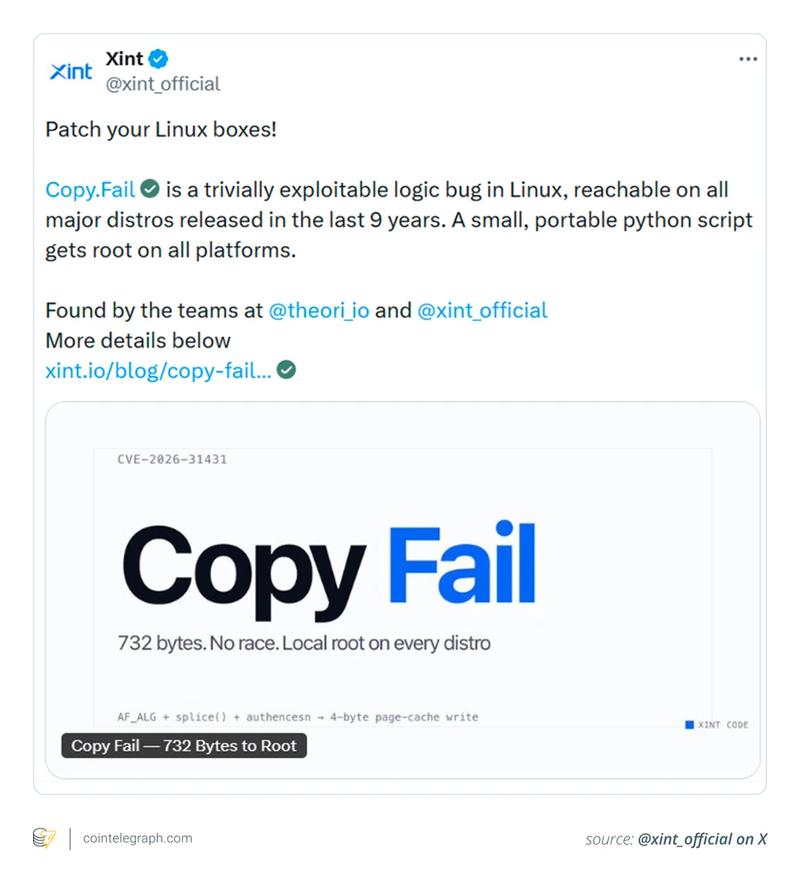
"Copy Fail" is the designation given to a local privilege-escalation security flaw found within the Linux kernel, discovered by cybersecurity experts at Xint.io and Theori.
Put simply, this vulnerability enables an adversary who has already obtained basic user-level system access on a Linux machine to upgrade their access rights to complete administrator or root authority. The vulnerability originates from a logic flaw in the kernel's management of specific memory operations embedded within its cryptographic modules. More specifically, a standard user account can manipulate the page cache, which serves as the kernel's temporary repository for frequently requested file information, in order to achieve elevated privileges.
The particularly concerning aspect of this security flaw is the simplicity with which it can be exploited. A streamlined Python script, needing only minor modifications, can consistently trigger the vulnerability across numerous different Linux configurations.
Security researcher Miguel Angel Duran states that exploiting affected systems requires approximately 10 lines of Python code to achieve root access.

3. Why this vulnerability stands out as particularly risky
Security vulnerabilities in Linux systems vary widely, ranging from sophisticated attacks requiring multiple chained exploits to more straightforward ones needing specific circumstances. "Copy Fail" has attracted considerable attention due to the minimal effort required once an initial system foothold has been established.
Critical factors that make this vulnerability particularly dangerous include:
- It impacts the majority of popular Linux distributions currently in use.
- A functional proof-of-concept exploit has been made publicly accessible.
- The vulnerability has been present in kernel versions dating back to 2017.
This combination of factors significantly elevates the threat level. Once exploit code becomes available on the internet, malicious actors can rapidly identify and target systems that have not been patched.
The reality that such a severe security flaw remained undetected for multiple years illustrates how even mature and widely-adopted open-source software projects can harbor subtle vulnerabilities deep within their core codebase.
Did you know? The Bitcoin white paper was released in 2008, but Linux dates back to 1991. That means much of today's crypto infrastructure is built on software foundations older than many blockchain developers themselves.
4. How the "Copy Fail" exploit works
To properly grasp the severity of this threat, one must first comprehend what complete "root" authority means within the context of a Linux server. Root privileges represent the ultimate level of control over any given machine.
Armed with root access, a malicious actor could:
- Install, modify or remove any software packages
- Access or exfiltrate sensitive files and cryptographic keys
- Alter essential system configurations
- Retrieve stored cryptocurrency wallets, private keys or authentication tokens if stored on the compromised system
- Disable firewalls, security monitoring applications or additional protective measures
The exploitation technique leverages vulnerabilities in how the Linux kernel administers its page cache mechanism. This system employs a compact, high-speed memory region to accelerate file access operations. Through manipulation of how the kernel processes cached file information, an adversary can deceive the kernel into providing higher access privileges than originally intended.
Importantly, this vulnerability cannot be exploited remotely from any location on the internet. The adversary must first obtain some level of access to the targeted system. This initial access might be acquired through various means such as a compromised user credential, an exploitable web application vulnerability or successful phishing campaigns. After securing that preliminary foothold, the attacker can rapidly escalate their access privileges to achieve complete root authority.
5. Why this matters for the cryptocurrency industry
Linux serves as the foundation for extensive cloud computing, server infrastructure and blockchain node operations, making it critically important to numerous cryptocurrency-related activities.
Essential components of the digital currency ecosystem depend on Linux, including:
- Blockchain validation nodes and complete node implementations
- Cryptocurrency mining operations and mining pool infrastructure
- Both centralized and decentralized cryptocurrency exchange platforms
- Custodial service providers and hot/cold wallet infrastructure systems
- Cloud-hosted trading platforms and liquidity provision systems
Given this extensive reliance, a kernel-level security flaw such as "Copy Fail" can generate indirect yet substantial exposure throughout the cryptocurrency sector. Should attackers successfully exploit this vulnerability on unprotected servers, potential ramifications include:
- Theft of private cryptographic keys or administrative access credentials
- Compromise of validator nodes leading to operational disruptions or enabling broader network-level attacks
- Unauthorized drainage of funds from hosted cryptocurrency wallets
- Triggering extensive service outages or deploying ransomware attacks
- Compromising user information maintained on vulnerable systems
Although the vulnerability does not directly target blockchain protocols themselves, successfully breaching the underlying server infrastructure supporting these systems can nonetheless result in substantial financial losses, damage to organizational reputation and significant operational interruptions.
Did you know? Major crypto exchanges rely on large-scale cloud, server and Kubernetes infrastructure to process trading activity, run blockchain nodes and support market-data operations around the clock. Coinbase, for example, has publicly described infrastructure tied to blockchain nodes, trading engines, staking nodes and Linux production environments.
6. Why initial access still poses a major threat in crypto environments
Certain users may minimize this vulnerability's significance because exploiting it requires a degree of pre-existing access to the targeted system. Nevertheless, the vast majority of genuine cyberattacks develop through multiple distinct stages rather than occurring instantaneously.
A standard attack progression typically follows this pattern:
- Adversaries initially penetrate systems through phishing operations, compromised passwords or malicious software applications.
- They establish a preliminary foothold with standard user-level access rights.
- They subsequently leverage vulnerabilities like "Copy Fail" to rapidly escalate privileges to complete administrator control.
- Following this, they extend their influence throughout the broader network infrastructure.
This attack methodology proves especially hazardous within the cryptocurrency domain, where exchange platforms, node operators and development organizations represent high-value targets for phishing campaigns and credential theft operations. An initially minor security breach can rapidly transform into a comprehensive system takeover when dependable privilege-escalation mechanisms are readily available.
7. Why security teams are particularly concerned
CISA's choice to add "Copy Fail" to its Known Exploited Vulnerabilities (KEV) catalog demonstrates that this security flaw is regarded as a critical-priority risk.
Warning indicators include the public availability of functional exploit code. Once proof-of-concept scripts become broadly accessible, malicious actors initiate automated scanning operations to identify unpatched systems for targeting.
Numerous organizations, especially those operating in financial services and cryptocurrency infrastructure, frequently postpone kernel updates. These entities prioritize maintaining system stability and preventing potential service disruptions or software compatibility problems. Unfortunately, this conservative approach can leave systems vulnerable for extended periods during critical security windows, providing adversaries with additional time to launch attacks.
Did you know? In simple terms, "root access" is like having the master key to an entire building. Once attackers gain it, they can potentially control nearly every process running on the system, change protected files and interfere with core security settings.
8. The AI connection: Why this vulnerability could signal bigger challenges ahead
Copy Fail's disclosure occurred during a period when the cybersecurity community is progressively concentrating on artificial intelligence's expanding role in vulnerability identification.
The disclosure timeline aligns with the launch of Project Glasswing, a cooperative initiative supported by prominent technology companies including Amazon Web Services, Anthropic, Google, Microsoft and the Linux Foundation. Project participants have emphasized how quickly evolving AI capabilities are becoming increasingly proficient at discovering and weaponizing security weaknesses within software code.
Anthropic has emphasized that state-of-the-art AI models are currently surpassing numerous human security experts in their ability to locate exploitable vulnerabilities in sophisticated software systems. The organization indicates these AI systems could substantially accelerate both offensive and defensive cybersecurity operations.
For the digital currency sector, this developing trend is especially worrying. Cryptocurrency platforms represent lucrative targets for cybercriminals and frequently rely on complex layered open-source technology stacks, potentially increasing their vulnerability as AI-powered attack techniques continue advancing.
9. What this means for everyday crypto users
For the majority of individual cryptocurrency holders, the immediate danger posed by this particular Linux vulnerability remains relatively minimal. Average users are not likely to become personally targeted.
However, indirect consequences could still impact users through:
- Security breaches or service interruptions at prominent exchange platforms
- Compromised custodial services maintaining user assets
- Attacks targeting blockchain validators or node service providers
- Disruptions affecting wallet services or trading platform infrastructure
Users practicing self-custody should pay attention if they:
- Operate their own Linux-powered blockchain nodes
- Manage personal validator systems or staking configurations
- Run cryptocurrency-related applications or servers on Linux platforms
In the final analysis, this situation emphasizes a crucial truth: Robust cryptocurrency security extends beyond secure smart contract design or consensus algorithm integrity. It equally depends on maintaining current and protected underlying operating systems, server infrastructure and supporting technological components.
10. How to stay protected
"Copy Fail" serves as a stark reminder of how rapidly fundamental operational security weaknesses can develop into significant security threats within the digital realm. The encouraging aspect is that the majority of these risks can be effectively managed. Both organizations and individual users can substantially minimize their vulnerability by promptly implementing security updates, enforcing more rigorous access control policies and upholding comprehensive cybersecurity best practices.
For cryptocurrency organizations and infrastructure teams
Companies operating Linux-based infrastructure should give priority to these protective measures:
- Install official security patches immediately upon their release
- Reduce and rigorously control local user accounts and permission levels
- Conduct regular security audits of cloud instances, virtual machines and physical server hardware
- Implement robust monitoring systems for detecting unusual privilege-escalation activity
- Enhance SSH access protocols, key-based authentication mechanisms and comprehensive login security
For everyday crypto users
Individual cryptocurrency holders can reduce their risk exposure by:
- Maintaining operating systems and all software with current updates
- Refraining from downloading content from unverified sources or unofficial cryptocurrency applications
- Utilizing hardware wallets for storing substantial cryptocurrency holdings
- Activating multi-factor authentication (MFA) on all available platforms
- Separating high-value wallet operations from routine computers and web browsers
For node runners, validators and developers
Individuals administering blockchain nodes or development infrastructure should:
- Install kernel and system updates immediately when available
- Actively monitor Linux security bulletins and advisory notifications
- Examine container configurations, orchestration platforms and cloud access permissions
- Restrict complete administrator privileges to the absolute minimum necessary