Hacker Steals $2.7M from Solv Protocol, Receives 10% Bounty Offer
According to cybersecurity experts in the cryptocurrency space, the attacker took advantage of a vulnerability that enabled unauthorized token minting, subsequently exchanging these illicitly obtained tokens for a Bitcoin-pegged asset.

Solv Protocol, a decentralized finance platform operating on Bitcoin infrastructure, has confirmed that an attacker successfully exploited one of its token vaults to the tune of $2.7 million, and the platform is now proposing a 10% bounty reward to the perpetrator in return for the restitution of the pilfered assets.
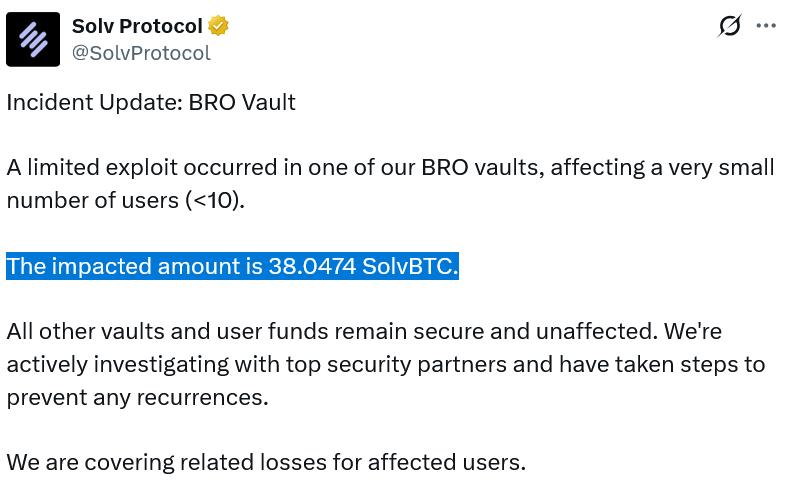
In a statement posted to X on Thursday, Solv disclosed that fewer than 10 users were affected by the security breach, while emphasizing its commitment to compensate the losses totaling 38.05 Solv Protocol BTC (SolvBTC), which is a token designed to maintain parity with Bitcoin (BTC).
According to the project's statement, protective countermeasures have now been deployed to ensure the identical attack vector cannot be exploited again, and a comprehensive investigation into the security breach is underway in collaboration with prominent crypto security companies Hypernative Labs, SlowMist and CertiK.
The platform enables participants to make Bitcoin deposits in exchange for Solv Protocol BTC, which subsequently provides them with the capability to engage in lending, borrowing or staking activities across various blockchain networks. With holdings of 24,226 Bitcoin valued at more than $1.7 billion, the project asserts its position as the most substantial on-chain Bitcoin reserve currently in existence.
While Solv has not yet provided official confirmation regarding the specific mechanics of the exploit, a pair of cryptocurrency security analysts have linked it to a weakness in one of Solv's smart contracts that permitted the attacker to generate excessive quantities of a token utilized within the protocol's ecosystem.
According to Chris Dior, co-founder of CD Security, the perpetrator leveraged this security flaw on 22 separate occasions before converting hundreds of millions of the minted tokens into slightly more than 38 SolvBTC.
A pseudonymous cryptocurrency analyst operating under the handle "Pyro" characterized the exploit as a re-entrancy attack, a technique where unanticipated inputs reveal weaknesses in smart contract code, representing a widely-used attack methodology that has compromised numerous DeFi protocols over recent years.
Within its X post, Solv provided an Ethereum wallet address as a means to incentivize the hacker toward agreeing to the 10% bounty proposal.
Nevertheless, based on data from Ethereum block explorer Etherscan, the attacker has not yet transmitted any on-chain communication to the specified address.