Ethereum's EIP-8105: Revolutionary encrypted mempool architecture unveiled
A comprehensive look at EIP-8105, a flexible encrypted mempool framework for Ethereum that conceals transaction details until block inclusion to combat harmful MEV extraction.
Every year, Ethereum users lose approximately $60 million to sandwich attacks. The public mempool exposes pending transactions before they're confirmed, enabling MEV bots to manipulate transaction ordering and inject their own transactions for financial gain. Despite years of debate and numerous attempts to address this issue through solutions outside the core protocol, the problem continues to plague the network to varying degrees.
One of the most promising approaches to combating MEV involves encrypting transactions in the mempool. Although this concept has been under active consideration for years, no protocol-level implementation has been achieved to date. Our previous research analyzed multiple threshold-encryption-based proposals, such as Shutter, Batched Threshold Encryption, and Flash Freezing Flash Boys. This article focuses on a meta-level proposal called "Universal Enshrined Encrypted Mempool (EIP-8105)".
How EIP-8105 approaches mempool encryption
The Universal Enshrined Encrypted Mempool, referred to as EIP-8105, represents a scheme-agnostic encrypted mempool architecture, enabling compatibility with various encryption methodologies including threshold encryption, MPC committees, TEEs, delay encryption, and fully homomorphic encryption. To enable this adaptable design, a novel system contract on the execution layer, designated as the key provider registry, is proposed. This registry would permit any account to register as a key provider responsible for holding and disclosing decryption keys through their preferred encryption technology.
How transactions are executed in Universal Enshrined Encrypted Mempool
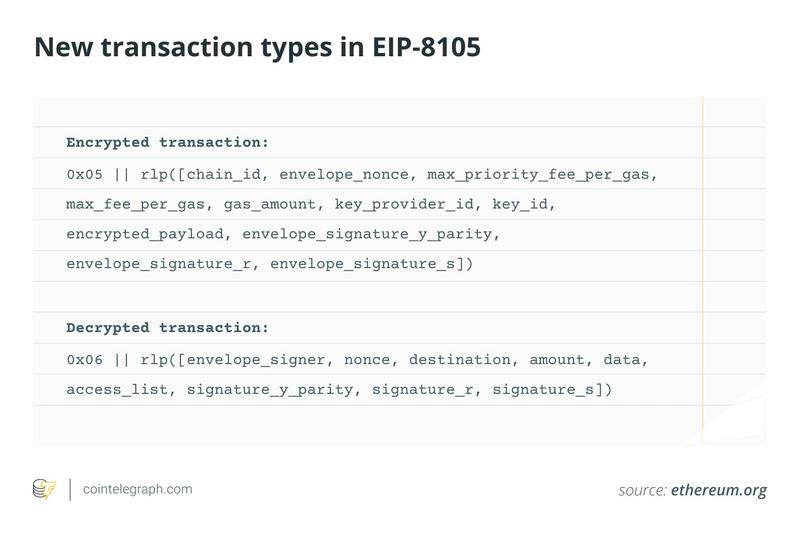
The Universal Enshrined Encrypted Mempool framework introduces two novel transaction types within the EIP-2718 framework: type 0x05 for encrypted transactions and type 0x06 for decrypted transactions. An encrypted transaction consists of an envelope containing an encrypted payload alongside a public payload, which includes the envelope nonce, gas amount, gas price parameters, key provider ID, key ID, and a signature. This particular structure is necessary to link the transaction with the selected key provider, allocate a nonce and guarantee that gas fees for the blockspace are accounted for.
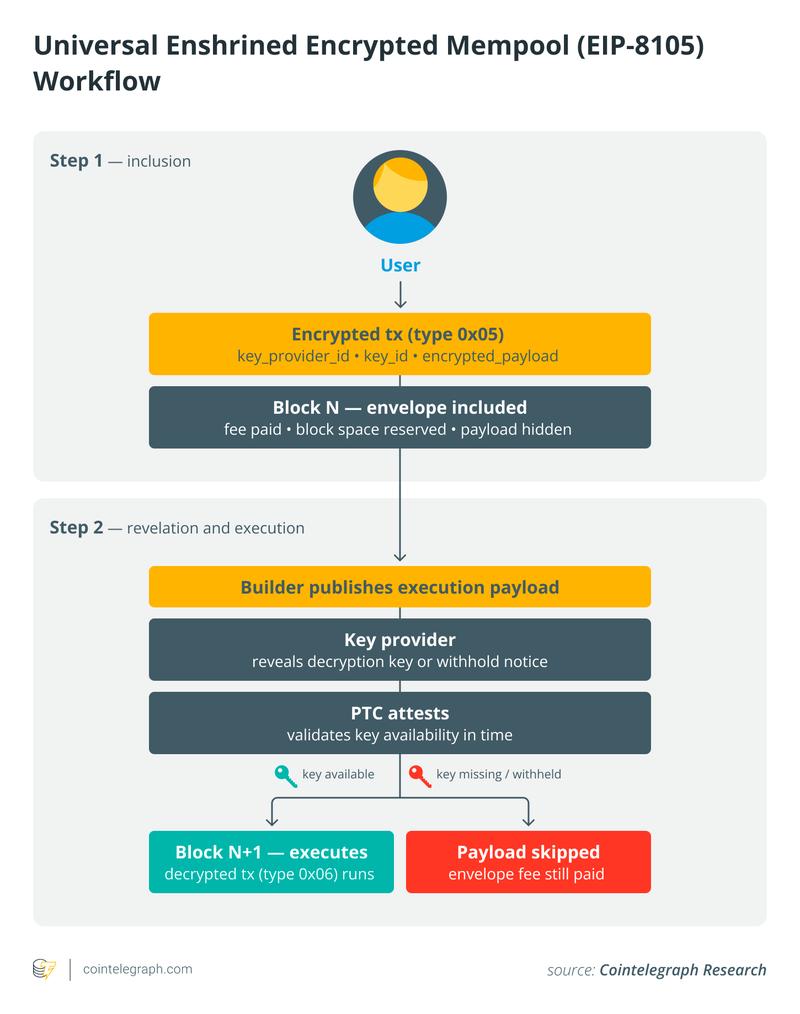
The EIP-8105 system operates through a two-step execution process. During the initial step, the encrypted transaction envelope gets incorporated into a block while the payload itself stays concealed. Key providers track transactions containing encrypted payloads, gather the associated transaction key IDs, and release either the matching decryption keys or a withhold notice after the block builder makes the data public.
Following the block builder's publication of the execution payload, the designated key provider discloses either the decryption key or issues a withhold notice. A Payload Timeliness Committee (PTC) oversees whether decryption keys associated with encrypted transactions are released punctually, verifies them, and confirms whether a valid key was available or absent. When the key is accessible and decryption is successful, the resulting decrypted transaction gets executed in the subsequent block. Should the key be unavailable, withheld, or if decryption fails, the decrypted payload is bypassed, though the envelope stays included, and the transaction fee remains payable.
The EIP additionally mandates a block structure that blocks MEV-extracting transactions from being introduced during the interval between decryption and execution. Decrypted transactions are required to appear at the block's beginning, plaintext transactions stay in the middle section, and encrypted transactions are positioned at the end. This arrangement ensures encrypted payloads are disclosed and executed exclusively after inclusion, simultaneously preventing secondary MEV.
Although EIP-8105 substantially reduces MEV exposure, key providers appearing earlier in the block maintain a restricted capacity to extract MEV from subsequent transactions through selective revelation or withholding of their decryption keys. The proposal seeks to address this vulnerability by allowing key providers to designate other trusted providers and arranging transactions based on the resulting key provider trust graph.
Encrypted Mempools and Ethereum's Roadmap
Encrypted mempools are gaining prominence as an essential component of Ethereum's roadmap, as the community searches for protocol-level mechanisms to diminish harmful MEV. Although EIP-8105 is no longer being promoted as one of the flagship features for the first 2027 hard fork, it continues to exist as an open draft, and its concepts keep shaping the wider initiative to develop a premier encrypted-mempool proposal for the upgrade.