CertiK Sounds Alarm: OpenClaw AI Agents Pose Severe Threat to Cryptocurrency Wallets Through 'Malicious Skills'
CertiK's analysis reveals that OpenClaw's explosive expansion resulted in severe security flaws that put API credentials, cryptocurrency wallets, and sensitive personal information at significant risk.

According to cybersecurity company CertiK, the expanding adoption of artificial intelligence assistants like OpenClaw presents serious security threats that leave users vulnerable to unauthorized activity, exposure of sensitive data, system infiltration, and the draining of cryptocurrency holdings.
OpenClaw operates as a self-hosted artificial intelligence agent capable of connecting with communication platforms including WhatsApp, Slack, and Telegram, while autonomously executing tasks on user devices such as handling electronic correspondence, scheduling appointments, and organizing documents.
Data from Openclaw.vps suggests approximately 2 million users actively engage with the platform each month. Research conducted by McKinsey in November showed that 62% of those surveyed indicated their companies were currently testing AI agent technology.
CertiK, however, cautions that the platform has evolved into a "primary supply chain attack vector at scale."
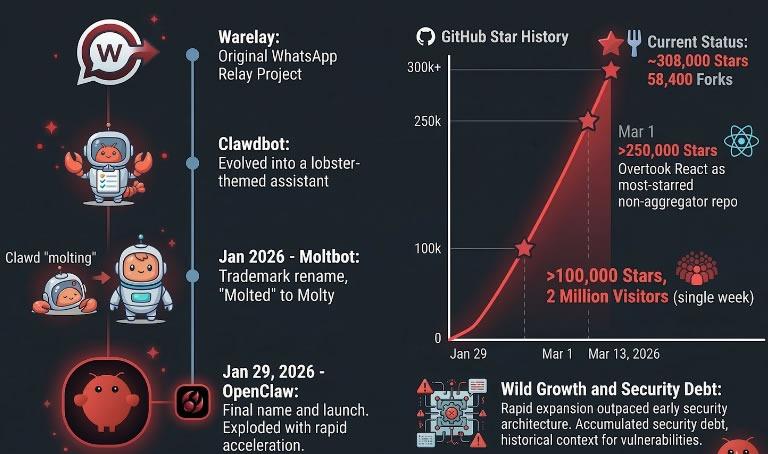
The platform evolved from a smaller initiative known as Clawdbot, which debuted in November 2025, eventually accumulating more than 300,000 GitHub stars—a bookmark or approval mechanism on the development platform—demonstrating explosive growth in user interest while simultaneously building up substantial "security debt" along the way, CertiK observed.
Yet, mere weeks following its introduction, Bitsight discovered 30,000 publicly accessible OpenClaw installations, and researchers at SecurityScorecard uncovered 135,000 deployments spanning 82 nations, with 15,200 of these particularly susceptible to remote code execution attacks.
The platform has additionally emerged as the most "aggressively scrutinized AI agent platform from a security standpoint," gathering over 280 GitHub Security Advisories, 100 Common Vulnerabilities and Exposures (CVEs), and experiencing a "string of ecosystem-level attacks" following its November debut, according to CertiK researchers in a report they provided to Cointelegraph.
Cryptocurrency wallet authentication data under threat
Given that OpenClaw functions as a connector between outside inputs and execution on local systems, "it introduces classic attack vectors," researchers explained.
Among these threats is local gateway hijacking, a scenario where malicious web pages or harmful code could take advantage of the agent's access to local machines to steal sensitive information from users or run unauthorized operations.
The cybersecurity firm highlighted concerns regarding plugins, which have the capability to introduce channels, tools, HTTP routes, services, and providers, while dangerous skills might be deployed from either local repositories or marketplace platforms.
Different from conventional malicious software, "malicious skills" possess the ability to alter behavior using natural language, making them resistant to traditional detection methods.
"Once launched, the malware can exfiltrate sensitive information such as passwords and cryptocurrency wallet credentials."
Dangerous backdoor mechanisms might also be concealed inside seemingly legitimate functional code repositories, "where they fetch seemingly benign URLs that ultimately deliver shell commands or malware payloads," researchers noted.
Researchers from CertiK informed Cointelegraph that threat actors deliberately distributed malicious skills throughout numerous valuable categories, "including utilities for Phantom, wallet trackers, insider-wallet finders, Polymarket tools, and Google Workspace integrations."
"They cast a remarkably wide net across the crypto ecosystem, with the primary payload designed to target a large number of browser extension wallets simultaneously, such as MetaMask, Phantom, Trust Wallet, Coinbase Wallet, OKX Wallet, and many others," they said.
According to the research team, there existed a "clear overlap in tradecraft with the broader crypto-theft ecosystem, like social engineering, fake utility lures, credential theft, wallet-focused phishing."
"These are all well-known plays from the crypto drainer playbook, and we did see them used here."
Peter Steinberg, the creator of OpenClaw who has recently joined the team at OpenAI, stated that efforts are underway to enhance OpenClaw's security infrastructure.
"Something that we worked on for the last two months is security. So things are a lot better on that front," said Steinberg at the "ClawCon" event on Monday in Tokyo.
OpenClaw installation not recommended for non-technical users
During the early part of this month, OX Security, a cybersecurity organization, documented a phishing operation that leveraged fraudulent GitHub postings and a counterfeit "CLAW" token to trick OpenClaw developers into linking their cryptocurrency wallets.
The recommendation from CertiK to everyday users "who are not security professionals, developers, or experienced geeks," is to refrain from installing and operating OpenClaw from the ground up, suggesting instead they hold off for "more mature, hardened, and manageable versions."
Security firm SlowMist unveiled a comprehensive security framework designed specifically for AI agents in early March, presenting it as a "digital fortress" intended to protect against dangers associated with autonomous systems managing onchain transactions and digital currency holdings.