Inactive Bitcoin Holdings May Become Prime Targets in Quantum Computing Age
Inactive Bitcoin holdings could represent the greatest vulnerability to quantum computing threats due to publicly visible keys and extended timeframes available to potential attackers. Discover why these wallets present the most significant concern.

The quantum threat to inactive Bitcoin addresses explained
Popular discourse about quantum computing's potential effect on Bitcoin typically centers on an apocalyptic scenario where the entire system fails simultaneously. This viewpoint, however, misses an important nuance regarding how the danger is truly allocated across the network.
The quantum risk facing Bitcoin is not uniformly distributed. Rather, it concentrates specifically in inactive addresses where public keys have already been revealed. This category encompasses numerous early coins from Bitcoin's genesis period and abandoned wallet holdings.
Contemporary Bitcoin (BTC) addresses benefit from enhanced protective mechanisms, yet these historical holdings may emerge as the principal objectives for early-generation advanced quantum computing systems. Such wallets present adversaries with temporal advantages, volume opportunities and limited defensive countermeasures. This unique convergence positions them as the most probable initial point of attack for any forthcoming quantum-based exploitation.
Critically, this scenario does not indicate an immediate system-wide catastrophe. Rather, it points toward a stratified vulnerability framework where a particular subset of the circulating supply faces substantially greater exposure compared to remaining holdings.
The quantum conversation extends beyond merely assessing computational advancement. It equally concerns identifying which portions of Bitcoin already possess inherent structural weaknesses versus those capable of implementing protective measures before threats materialize.
Did you know? Dormant Bitcoin wallets may hold coins secured by older cryptographic methods, making them potential targets if quantum computers ever break current encryption standards.
Understanding what aspects of Bitcoin quantum computers could compromise
Bitcoin's security architecture rests upon two fundamental cryptographic pillars: hash functions (SHA-256) governing mining operations and block integrity, and public-key cryptography (ECDSA/Schnorr) controlling transaction authorization.
These cryptographic components face distinct quantum computing challenges.
Hash functions demonstrate considerable robustness. Although Grover's algorithm presents theoretical vulnerabilities, it would not completely compromise their utility. The practical outcome would involve diminishing their operational security threshold.
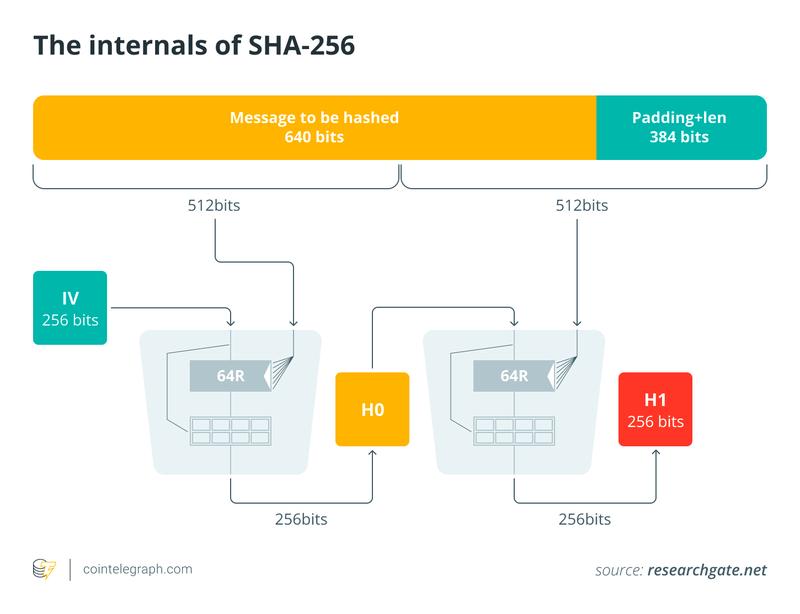
Public-key cryptography presents a contrasting vulnerability profile. Leveraging Shor's algorithm, sufficiently powerful quantum computing systems could calculate a private key when provided with its corresponding public key. Within Bitcoin's operational framework, this capability would enable attackers to transfer any cryptocurrency associated with an exposed public key.
Critical difference: Transaction-time versus static attacks
Comprehending why inactive wallets represent heightened risk requires distinguishing between two categories of quantum-based attacks:
Transaction-time attacks
- These attacks materialize when users initiate transaction broadcasts.
- Public keys become observable throughout the transaction lifecycle.
- Adversaries must calculate the private key within an abbreviated timeframe, approximately one block interval, typically around 10 minutes.
Static attacks
- These focus on cryptocurrency whose public keys already exist within blockchain records.
- Adversaries possess unlimited time, potentially spanning days, weeks or indefinitely longer, to perform private key calculations.
- No triggering transaction event is necessary.
This temporal distinction proves fundamental. Transaction-time attacks face speed limitations, whereas static attacks encounter only computational power constraints.
The heightened vulnerability of inactive wallets compared to active holdings
Inactive wallets possess three converging attributes that establish exceptional vulnerability: absence of protective measures, extended temporal exposure and concentrated high-value holdings.
- Absence of protective measures: Active wallets retain the capability to transfer assets to fresh addresses, implement improved security protocols or transition to forthcoming quantum-resistant architectures. Inactive wallets lack these options. When ownership access has been forfeited or activity has ceased entirely, those holdings remain indefinitely vulnerable.
- Extended temporal exposure: When a wallet's public key already appears in blockchain records, adversaries can perform calculations offline without temporal constraints. This eliminates a crucial Bitcoin defense mechanism: the brief transaction validation period.
- Concentrated high-value holdings: Numerous inactive wallets belong to pioneer Bitcoin participants who extracted or accumulated coins during periods of minimal valuation. Presently, certain wallets may contain BTC valued at tens of thousands of dollars. This establishes a high-reward, minimal-resistance attack surface.
Did you know? Coins in inactive wallets cannot upgrade their security, which means quantum-resistant fixes may protect only active users, not untouched early Bitcoin holdings.
Identifying the most vulnerable Bitcoin wallet categories
Bitcoin addresses do not share uniform vulnerability levels. The most exposed classifications encompass the following:
Legacy P2PK (Pay-to-Public-Key) outputs
- These predominated throughout Bitcoin's formative period.
- Public keys appear explicitly within blockchain data.
- They possess no supplementary protective mechanisms.
Address reuse patterns
- This occurs when users execute transactions from an address yet continue utilizing it subsequently.
- Public keys become observable following initial expenditure.
- All residual funds become susceptible.
Specific contemporary script formats
- Certain recent formats, including Taproot outputs, embed public keys directly.
- Despite being engineered for operational efficiency and transaction privacy, they may nonetheless fall within "static" exposure categories under quantum threat models.
Even comparatively more secure formats can forfeit that protection when users engage in address reuse behaviors.
Quantifying the problem: Inactive coins represent dominant risk category
Quantum vulnerability transcends theoretical speculation. It can be quantified through concrete exposure metrics.
Current assessments indicate the following:
- Bitcoin valued at millions of dollars persists in addresses featuring exposed public keys.
- Substantial portions of these holdings originate from early-period mining compensation.
- Numerous holdings have remained stationary for beyond a decade.
Considerable proportions of these holdings comprise 50 BTC block rewards from Bitcoin's nascent phase, frequently linked to miners who have discontinued participation.
This generates a structural asymmetry:
- A comparatively limited quantity of wallets
- Controlling a disproportionately substantial share of vulnerable cryptocurrency
Stated differently, the most attractive quantum targets simultaneously represent some of Bitcoin's largest holdings.
Did you know? Some of the largest Bitcoin holdings have not moved in more than a decade, creating a silent pool of assets that could be exposed to future quantum attacks.
A complex challenge: Inactive wallets and network governance considerations
Inactive wallets present complications extending beyond purely technical dimensions. They additionally generate governance and policy dilemmas.
Should quantum adversaries commence targeting these holdings, the Bitcoin ecosystem may confront challenging decisions:
- Should such cryptocurrency become claimable when cryptographic prerequisites are satisfied?
- Should protocol modifications seek to freeze or safeguard extensively dormant assets?
- How should the network classify assets that appear lost yet remain technically transferable?
This surfaces broader discussions surrounding ownership rights, protocol immutability and digital asset recovery. Unlike active participants, inactive wallets cannot engage in any migration or enhancement procedures, establishing them as a distinctive edge case within protocol architecture.
Why this scenario does not indicate Bitcoin's fundamental failure
Distinguishing between Bitcoin's long-range structural vulnerability and any imminent danger remains essential.
Presently, no broadly recognized evidence confirms that quantum computing systems capable of compromising Bitcoin's cryptographic foundation exist. The construction of such technology is anticipated to require years, potentially decades, of continued engineering advancement.
Furthermore:
- The vulnerability is anticipated to materialize incrementally.
- The ecosystem possesses adequate time to investigate and implement protective strategies.
- Active participants can adapt considerably faster than inactive wallets.
This indicates the initial consequences of quantum progress, should they arrive, may prove targeted rather than comprehensive.
Protective measures available currently
To diminish the susceptibility of inactive Bitcoin wallets to quantum exploitation, holders can implement several approaches:
- Minimizing public-key exposure: Curtailing address reuse and restricting when public keys are disclosed remains a fundamental best practice.
- Migration readiness: Establishing frameworks enabling users to relocate assets into future quantum-resistant formats will prove essential.
- Protocol research: Continuing investigation explores how Bitcoin might incorporate quantum-resistant cryptographic techniques without undermining its foundational characteristics.
These protective measures predominantly advantage active participants, thereby reinforcing the disparity between transferable and immovable cryptocurrency holdings.