North Korean hackers evolve from digital shadows to physical presence
The cyber operations of North Korea in cryptocurrency have evolved to include fraudulent IT workers, in-person conference networking, and sophisticated DeFi breaches that penetrate throughout the sector.

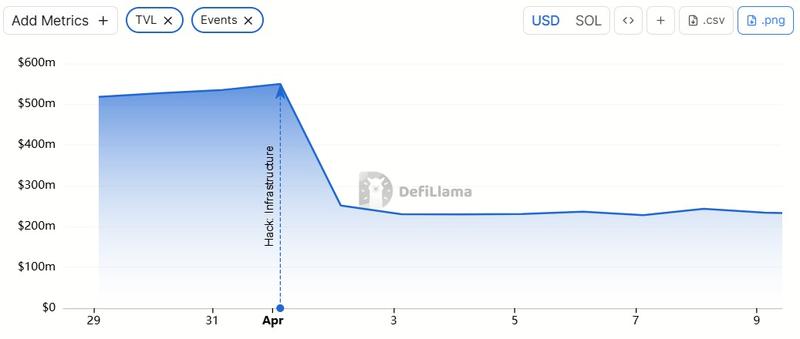
The $285 million breach targeting Drift, a decentralized exchange (DEX), this month marked the most significant cryptocurrency theft in more than a year, since the exchange Bybit suffered a $1.4 billion loss. State-sponsored hackers from North Korea emerged as the primary suspects behind both incidents.
Last autumn, the attackers disguised themselves as representatives of a quantitative trading firm and met with Drift's protocol team face-to-face at a prominent cryptocurrency conference, according to a Sunday X post from Drift.
"It is now understood that this appears to be a targeted approach, where individuals from this group continued to deliberately seek out and engage specific Drift contributors, in person, at multiple major industry conferences in multiple countries over the following six months," said the DEX.
Previously, North Korean cyber operatives have focused their efforts on crypto companies through digital means, utilizing virtual meetings and remote employment arrangements. A face-to-face interaction at an industry conference would ordinarily appear innocuous, but the Drift breach should serve as a wake-up call for participants to reassess connections established at recent gatherings.
North Korea expands crypto playbook beyond hacks
TRM Labs, a blockchain forensics company, characterized the event as 2026's largest DeFi breach (thus far) and the second-biggest exploit in the history of Solana, trailing only the $326 million Wormhole bridge attack in 2022.
The first contact occurred approximately six months prior, but the actual exploit can be traced to mid-March, based on TRM's analysis. The perpetrator initiated operations by transferring funds from Tornado Cash and launching the CarbonVote Token (CVT), while employing social engineering techniques to convince multisig signers to authorize transactions that granted elevated permissions.
Subsequently, they fabricated legitimacy for CVT by creating a substantial supply and artificially inflating trading volume to mimic genuine demand. The oracles used by Drift detected this activity and categorized the token as a legitimate asset.
Once the pre-authorized transactions were carried out on April 1, CVT was recognized as collateral, withdrawal thresholds were raised and funds were extracted in actual assets, including USDC.
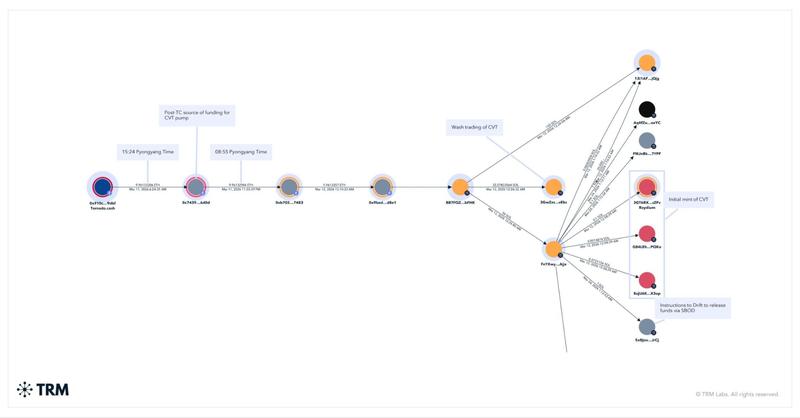
TRM reported that the velocity and intensity of the laundering operations that followed surpassed those observed in the Bybit breach.
There is widespread belief that North Korea leverages massive crypto heists like the Drift and Bybit incidents in conjunction with more extended strategies, such as positioning operatives in remote positions at technology and cryptocurrency companies to create consistent revenue streams. According to the United Nations Security Council, these funds support the nation's weapons development program.
Taylor Monahan, a security researcher, stated that the penetration of DeFi protocols can be traced back to "DeFi summer," noting that approximately 40 protocols have been in contact with individuals suspected of being DPRK operatives.
North Korean state media announced Thursday that the nation conducted tests of an electromagnetic weapon and a short-range ballistic missile, designated as the Hwasong-11, equipped with cluster munition warheads.
Infiltration network fuels steady crypto revenue
An independent investigation uncovered how an interconnected group of IT workers with North Korean connections generated millions of dollars through sustained infiltration operations.
Information acquired from an unnamed source and distributed by ZachXBT demonstrated the network masquerading as software developers and integrating themselves throughout cryptocurrency and technology companies, producing approximately $1 million monthly and exceeding $3.5 million since November.
The collective obtained employment using fraudulent identities, channeled payments through a unified system, subsequently converted funds to fiat currency and transferred them to Chinese bank accounts through platforms such as Payoneer.
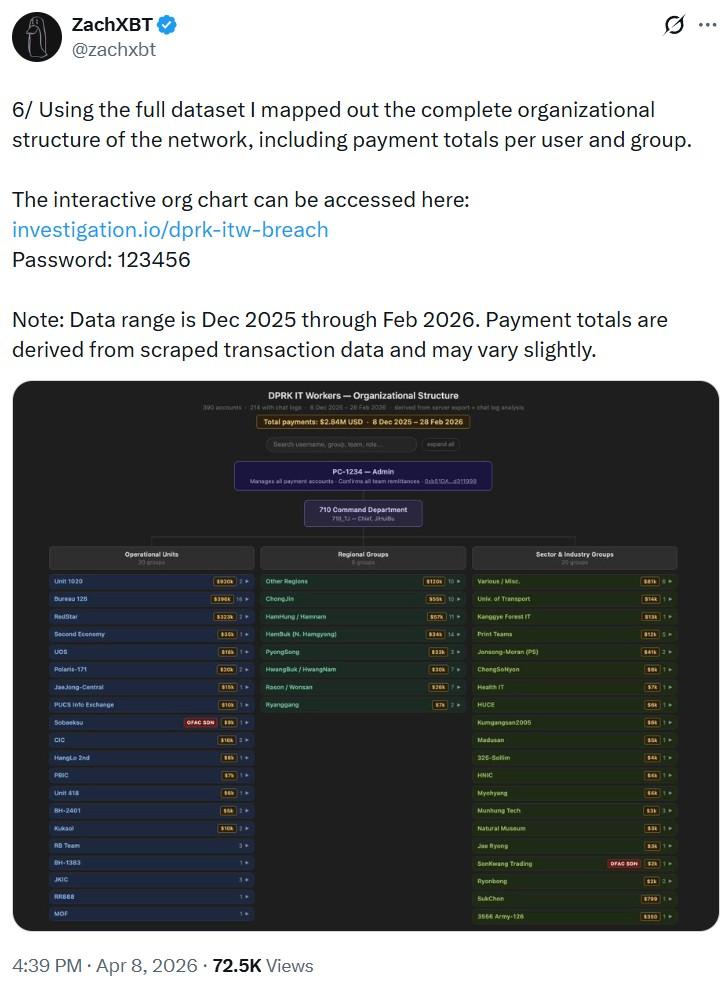
The scheme depended on rudimentary infrastructure, featuring a communal website with a universal password and internal ranking systems monitoring earnings.
The operatives submitted applications for positions openly using VPNs and counterfeit documentation, indicating a more comprehensive strategy of placing agents to secure continuous revenue.
Defenses evolve as infiltration tactics spread
Cointelegraph experienced a comparable operation in a 2025 investigation directed by Heiner García, who maintained contact with a suspected operative for several months.
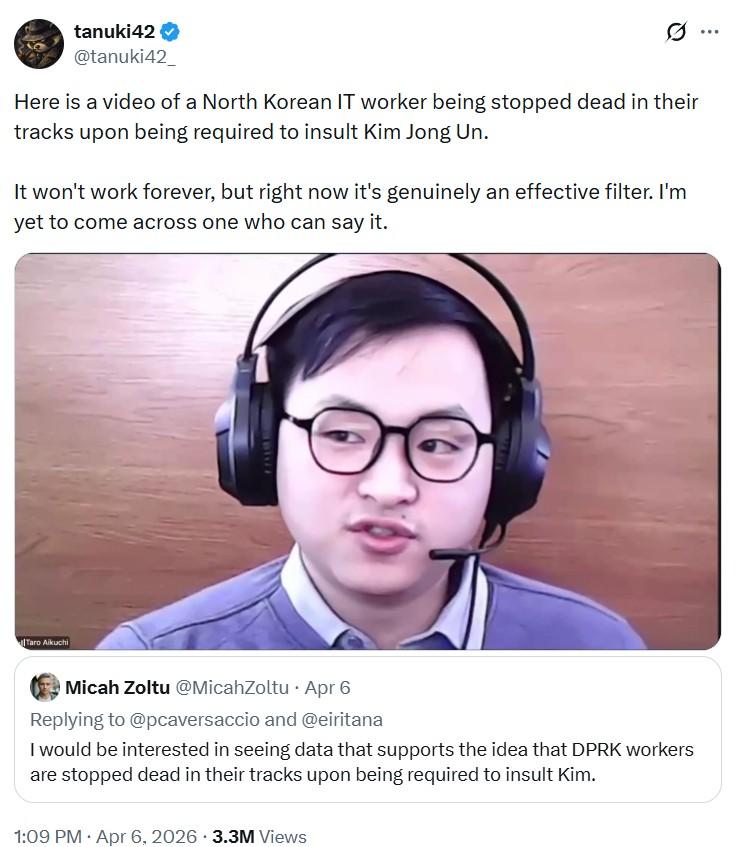
Cointelegraph subsequently participated in García's mock interview with a suspect who identified himself as "Motoki," claiming Japanese nationality. The suspect abruptly terminated the call after being unable to introduce himself in his purported native dialect.
The investigation discovered that operatives circumvented geographical limitations by utilizing remote access to devices physically situated in nations such as the US. Rather than employing VPNs, they controlled those machines directly, causing their activity to seem domestic.
At this point, technology recruiters have recognized that the individual on the opposite end of a virtual job interview could very well be a North Korean cyber operative. A strategy that has gone viral involves asking suspects to insult Kim Jong Un. To date, the approach has proven successful.
Nevertheless, given that Drift was contacted in person and García's research revealed operatives discovering innovative approaches to circumvent geographical restrictions, North Korean actors have persistently adapted to the cat-and-mouse dynamic.
Asking job candidates to refer to North Korea's supreme leader as a "fat pig" represents an effective tactic for now, but security researchers caution that this won't remain effective indefinitely.