North Korea's Lazarus Group Deploys New macOS Malware Targeting Cryptocurrency and Financial Technology Companies
Cybersecurity experts have discovered that the 'Mach-O Man' malware toolkit is connected to Lazarus Group operations, employing fraudulent video conference invitations and ClickFix techniques to compromise macOS systems and harvest sensitive credentials from corporate networks.

Cybersecurity experts have identified a newly discovered macOS malware operation with ties to the Lazarus Group, the notorious North Korean state-sponsored hacking collective responsible for orchestrating numerous high-profile cryptocurrency heists throughout the industry.
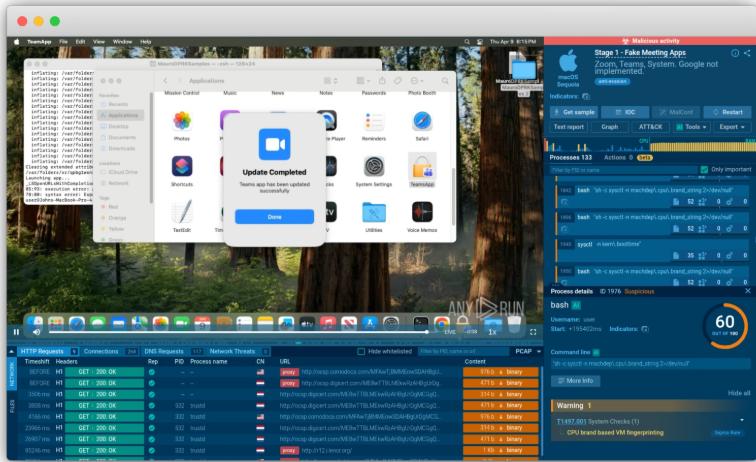
Discovered and reported on Tuesday, this sophisticated "Mach-O Man" malware toolkit is being disseminated through "ClickFix" social manipulation tactics targeting both conventional enterprises and cryptocurrency organizations, as reported by Mauro Eldritch, an offensive security specialist and the founder of threat intelligence firm BCA Ltd.
Targeted individuals are deceived into joining fraudulent Zoom or Google Meet video conferences where they receive instructions to run specific commands that covertly download the malicious software in the background, enabling threat actors to circumvent conventional security measures undetected and obtain access to login credentials and enterprise networks, according to the security expert's Tuesday analysis.
According to the researchers, this attack campaign has the potential to result in compromised accounts, illegitimate infrastructure penetration, monetary damages and the leakage of sensitive information, highlighting how Lazarus persistently broadens its attack scope beyond cryptocurrency-focused enterprises.
The Lazarus Group stands as the primary culprit in several of the most significant cryptocurrency security breaches on record, including the $1.4 billion compromise of Bybit exchange in 2025, representing the industry's most substantial breach to date.
"Mach-o Man" kit seeks to implement hidden stealer malware
The concluding phase of this attack operation involves a data theft tool engineered to harvest browser extension information, saved browser login credentials, cookies, macOS Keychain records and additional confidential data from compromised systems.
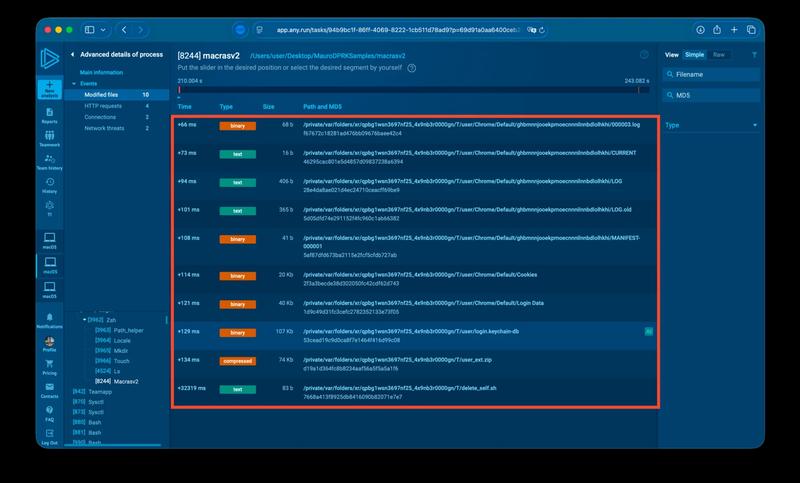
Following the data collection process, the stolen information is compressed into a zip archive and transmitted via Telegram to the threat actors. Subsequently, the malware's automated removal script eliminates the complete toolkit utilizing the system's rm command, which circumvents user verification and permission requirements during the file deletion process.
The innovative malware toolkit was reverse-engineered by the cybersecurity specialist leveraging the macOS analysis features provided by cloud-based malware sandbox platform Any.run.
Earlier in April, North Korean hackers used AI-enabled social engineering schemes to steal about $100,000 worth of funds from crypto wallet Zerion, after gaining access to some team members' logged-in sessions, credentials and the company's private keys, Cointelegraph reported on April 15.