Security researcher's warning ignored before ZetaChain's $334K hack
A security researcher had identified and reported the critical flaw that enabled ZetaChain's $334,000 hack through the platform's bug bounty program prior to the incident, though the submission was rejected by the team.

The security flaw that enabled the recent ZetaChain exploit had previously been submitted through the platform's bug bounty initiative prior to the attack occurring, though it was rejected by the team who characterized it as intended functionality.
According to a post-mortem analysis released on Wednesday, the team indicated that this incident has triggered an internal examination of their bug bounty submission handling procedures, with particular emphasis on reports detailing chained attack vectors that might seem benign when examined separately but become critical when combined together.
"This bug was reported and they simply ignored it. That's how bug bounty programs work with these protocols currently; they incentivize losses for the protocol, the TVL, and the user's balance instead of paying the researcher for discovering and fixing the bug."
On Sunday, ZetaChain experienced a carefully planned exploit that resulted in losses of roughly $334,000, with the attack focusing on the platform's cross-chain gateway contract. The malicious actor extracted funds through nine separate transactions spanning four different blockchain networks, specifically Ethereum, Arbitrum, Base and BSC, with all stolen funds coming from ZetaChain-controlled wallet addresses. The incident did not impact any user-held funds.
Attacker exploits small design flaws
According to ZetaChain's post-mortem analysis, the malicious actor took advantage of three separate design weaknesses that, when considered independently, could have appeared insignificant, but when combined created a pathway to completely drain the affected wallets. The first weakness was that the gateway permitted anyone to transmit arbitrary cross-chain instructions without any limitations. The second issue was that on the destination side, the system would execute virtually any instruction on any smart contract, protected only by a blocklist that was so limited it failed to catch basic token transfer operations.
The third vulnerability involved wallet addresses that had previously interacted with the gateway and still maintained unlimited spending authorizations that were never revoked or removed. Through the combination of these three separate weaknesses, the attacker was able to simply instruct the gateway to move tokens from compromised wallets to addresses under their control, and the gateway executed these instructions without resistance.
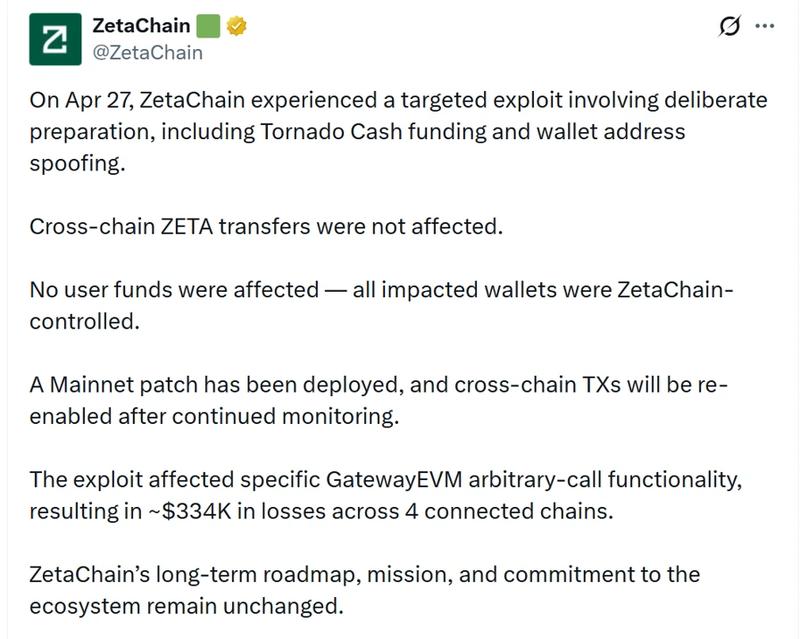
"This was not an opportunistic attack," ZetaChain stated in their post-mortem assessment. The malicious actor financed their wallet address using Tornado Cash three days in advance of executing the exploit, created a custom-designed drainer contract deployed on the ZetaChain network and conducted an address poisoning operation before inserting it into their transaction record through dust transfers.
ZetaChain further noted that a security patch that permanently deactivates the arbitrary call functionality is currently being deployed across mainnet nodes. The platform has also eliminated unlimited token approvals from its deposit mechanism, substituting them with exact-amount approvals for all future transactions.
AI DeFi exploit success rate increases
A recent research study conducted by a16z examined whether a commercially available AI agent could move beyond simply detecting DeFi vulnerabilities to actually generating functional exploits. Utilizing OpenAI's Codex against a collection of 20 authentic Ethereum price manipulation incidents, the research team operated the agent within a sandboxed testing environment with no access to future transaction information and no instruction on the mechanics of how the attacks functioned. The agent achieved success in only 10% of cases.
Nevertheless, when the research team provided the agent with organized knowledge regarding common attack methodologies and exploit execution workflows, the success rate increased dramatically to 70%.