Privacy alarms raised over White House mobile application's location monitoring capabilities
An official mobile application from the White House designed for news notifications has triggered privacy debates due to its apparent capabilities for tracking user locations and gathering personal information.
Privacy and security worries have emerged surrounding a newly released mobile application from the United States government, with users and technical experts flagging possible location-monitoring capabilities, data harvesting practices and security weaknesses.
The mobile application was introduced by the White House on Friday, positioned as a means for citizens to establish a "direct line to the White House," offering features such as breaking news notifications about significant governmental declarations, access to livestream content and updates regarding "policy breakthroughs."
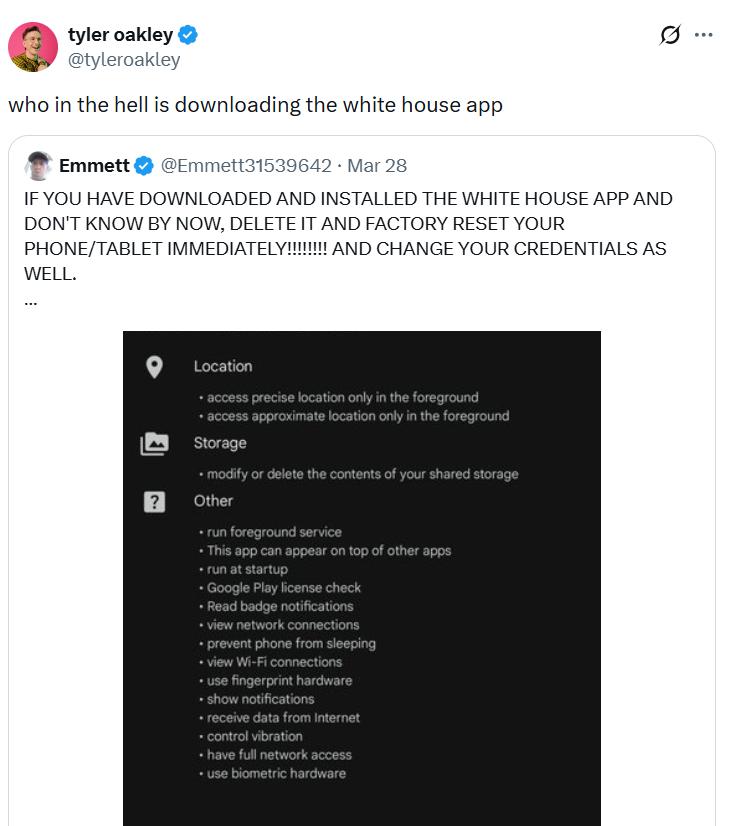
Nevertheless, social media users on X have voiced apprehensions regarding the various permissions that the application demands to function, which reportedly encompass access to location services, shared device storage and monitoring of network activity, although independent verification of these assertions remains pending.
Though numerous mobile applications routinely seek location access and maintain logs of user activity, an application released under the authority of the federal government requesting such sensitive information naturally generates heightened scrutiny and concern.
That said, the current listings available on both the Google Play Store and Apple's App Store do not presently show these particular warnings.
Cointelegraph has reached out to the White House seeking official commentary on these matters.
Security engineer says GPS tracking is part of the app
According to information displayed on the application's Google Play Store listing, personal information such as telephone numbers and email addresses could potentially be gathered during the download process and subsequent usage. Apple's App Store listing, by contrast, provides a link directing users to review the White House's privacy policy documentation.
A software development professional operating under the X username Thereallo, together with Adam, who works as a security engineer and infrastructure architect, claim to have discovered programming code indicating the application may have the ability to access a device's GPS functionality for location monitoring purposes.
Although such functionality is widespread among many mobile applications, Adam noted that the presence of location-tracking services appears peculiar in software that seemingly has no requirement for such capabilities.
"There is no map, no local news, no geofencing, no events near you, no weather. Nothing in the app that requires location," he added.
Concerns of GPS tracking every 4.5 minutes
Thereallo presented similar assertions, stating the application contains programming code that could potentially enable location monitoring of a device at intervals of every 4.5 minutes when actively running in the foreground and every 9.5 minutes when operating in the background, although independent confirmation of this claim has not yet been established.
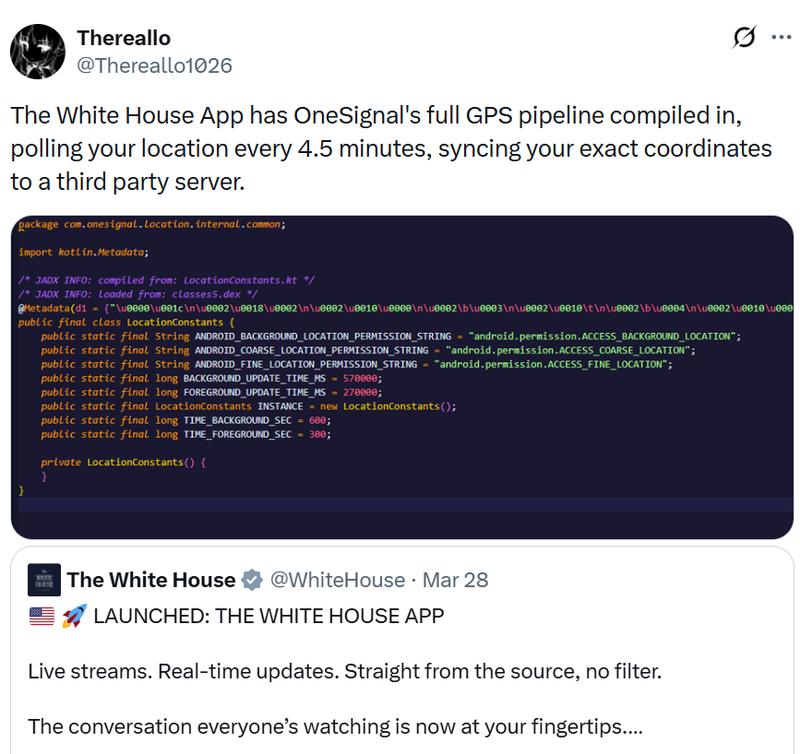
Their analysis revealed that while the functionality currently requires user permission to activate, they cautioned that it remains only "one call away from activating," emphasizing that the underlying tracking "infrastructure is there, ready to go."
Additionally, Thereallo indicated the application is gathering various other forms of data including user interactions with notifications, clicks on in-app messaging, telephone numbers and state information.
Security could be broken, Adam says
According to Adam's assessment, the application's security infrastructure may be insufficiently robust, potentially allowing an individual with adequate technical expertise to intercept transmitted data or modify the app's operational behavior.
"Anyone on the same Wi-Fi network, say, at a coffee shop, an airport, or a congressional hearing room, can intercept API traffic with a proxy. Anyone with a jailbroken device can hook and modify the app's behavior at runtime," he said.
"No servers were probed. No network traffic was intercepted. No DRM was bypassed. No tools were used that require jailbreaking. Everything described here is observable by anyone who downloads the app from the App Store and has a terminal."