Gmail's Dot Alias Feature Exploited in Sophisticated Robinhood Phishing Attack
A sophisticated phishing campaign targeting Robinhood customers has emerged, exploiting Gmail's dot alias functionality combined with vulnerabilities in Robinhood's user registration process to deliver fraudulent emails directly from legitimate servers.

A sophisticated phishing campaign targeting Robinhood customers has emerged, leveraging Gmail's built-in "dot alias" functionality alongside vulnerabilities in Robinhood's user registration process to distribute fraudulent emails to unsuspecting victims.
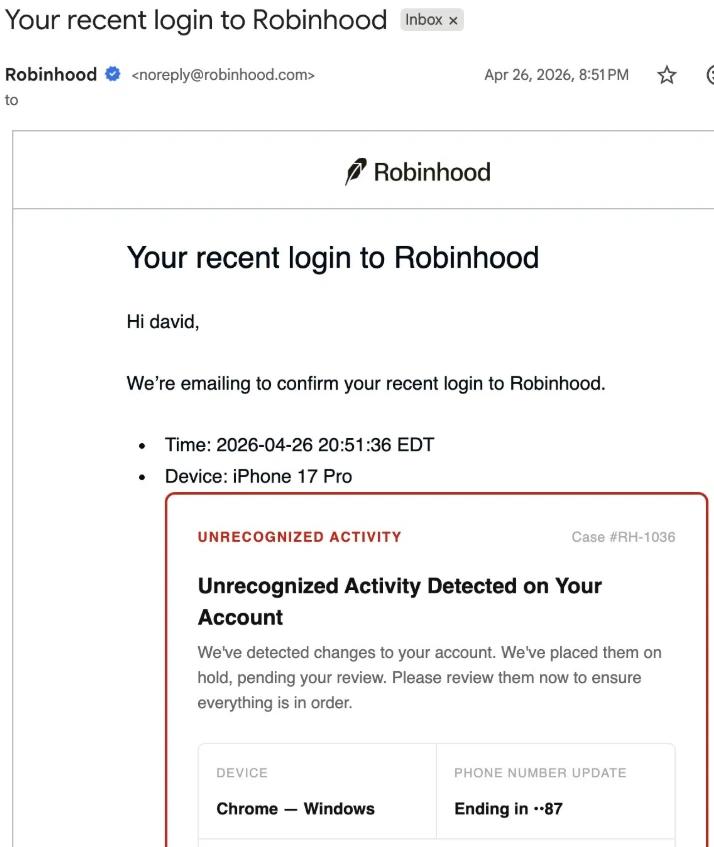
Reports from Robinhood customers surfaced on social media platforms on Sunday, detailing emails that appeared to originate from the company's legitimate mail server. These messages alerted recipients about unauthorized device logins and contained "call to action" buttons that directed users to fraudulent websites designed to steal credentials.
According to Alex Eckelberry, a cybersecurity researcher and tech CEO, the phishing operation didn't result from any security breach. Instead, attackers exploited a native Gmail feature that disregards periods in email addresses, combined with what he described as a "couple of terrible holes" in Robinhood's account setup.
The campaign emerges following a report from blockchain security company Hacken released earlier this month, which revealed that phishing and social engineering attacks were the predominant threat in crypto attacks during the first quarter of 2026, resulting in $306 million in losses.
Hackers created fake Robinhood accounts
According to Eckelberry, the fraudulent scheme depended on attackers establishing accounts on Robinhood using email addresses that closely resembled those of their intended victims.
As an illustration, a Robinhood customer might use an email address like "jane.smith@gmail.com." An attacker would then register a new Robinhood account using the same email but without the period, such as "janesmith@gmail.com."
Although Robinhood's system would recognize these as two distinct accounts, Gmail's infrastructure disregards periods in the username portion of email addresses. As a result, attackers could trigger Robinhood to send automated emails for their fraudulent account, which would then be delivered to the victim's inbox instead.
To inject a malicious link into the automated email that Robinhood sends when a new account is established, the attackers would insert HTML code into the optional "device name" field on Robinhood's platform, which Gmail's system interprets as formatting commands.
"The result is a real email from 'noreply@robinhood.com' that passes SPF, DKIM, and DMARC. It looks completely legitimate but now contains injected fake warning text and a working phishing button. Clicking the button leads to a fake login site," Eckelberry said.
The email is only dangerous if information is added
According to Eckelberry, simply accessing the fraudulent login website isn't sufficient for hackers to compromise an account. However, if users provide sensitive credentials such as passwords on these fake sites, malicious actors could potentially gain unauthorized access.
On Monday, Robinhood's support account on X released a statement acknowledging that certain users had received a fraudulent email originating from "noreply@robinhood.com" with the subject line "Your recent login to Robinhood" and attributed the incident to an exploitation of the "account creation flow."
"This phishing attempt was made possible by an abuse of the account creation flow. It was not a breach of our systems or customer accounts, and personal information and funds were not impacted," they said.
"If you received this email, please delete it and do not click any suspicious links. If you have clicked a suspicious link or have any questions about your account, please contact us directly within the Robinhood app or website."