April Crypto Heists Totaling $578M Linked to North Korean Actors Following Kelp DAO Attack
Cryptocurrency thefts connected to DPRK surpassed $578M throughout April following the Kelp DAO security breach, with attacks spreading across DeFi platforms, corporate entities and individual users.

A $292 million security breach hit Kelp DAO on Saturday, surpassing Drift to become the year's largest cryptocurrency exploit to date. Hackers with suspected ties to North Korea are believed to be responsible for the attack.
On Monday, Kelp DAO attributed the exploit to an infrastructure failure within LayerZero's cross-chain messaging protocol. In response, LayerZero pointed to Kelp DAO's implementation of a single verifier configuration for approving cross-chain messages as the vulnerability that enabled the breach.
According to LayerZero, "preliminary indicators" connected the exploit to TraderTraitor, which operates as a subgroup within the North Korean state-sponsored hacking organization known as Lazarus Group.
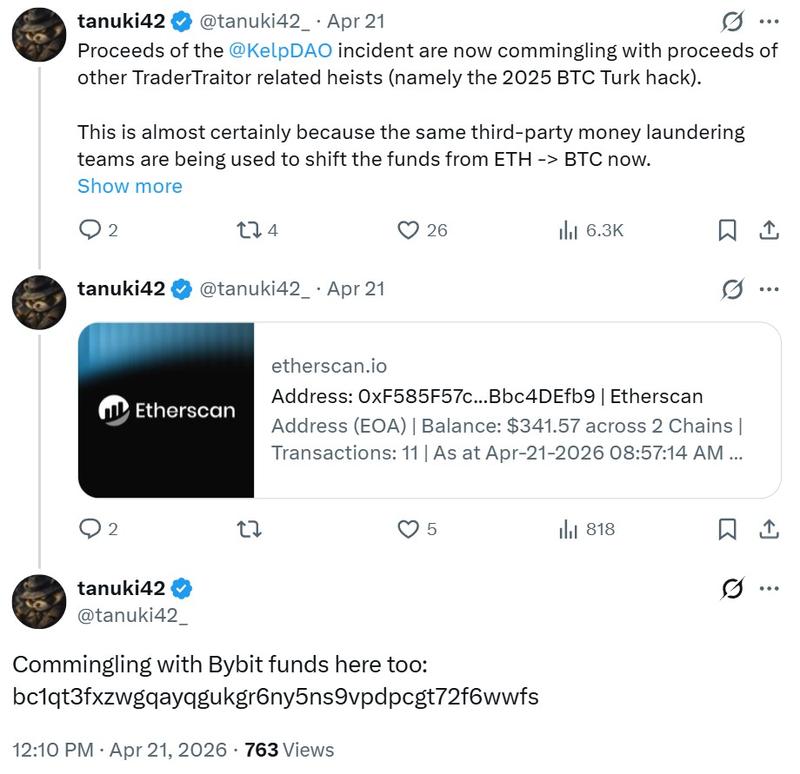
Blockchain investigator Tanuki42's analysis similarly identified connections to TraderTraitor. On Tuesday, Tanuki42 revealed that assets stolen during the Kelp DAO incident have been mixed with funds from previous exploits attributed to the same threat actors.
Although North Korea's cyber operations targeting decentralized finance platforms have intensified throughout April, the tactics employed by these groups also represent a significant risk to corporate organizations and individual users.
North Korea's crypto schemes back in focus
The decentralized exchange Drift suffered an April Fools' Day exploit that resulted in $285 million in losses, pushing suspected North Korea-linked cryptocurrency theft to a minimum of $578 million across significant incidents during the month.
These two incidents represent the most substantial crypto heists attributed to North Korean threat actors since the security breach at Bybit.
At this point, the cryptocurrency industry has become aware that DPRK-affiliated operatives masquerade as IT developers to obtain remote positions at technology companies. Both security researchers and the United Nations indicate that this strategy generates millions of dollars in funding for North Korea's weapons development programs.
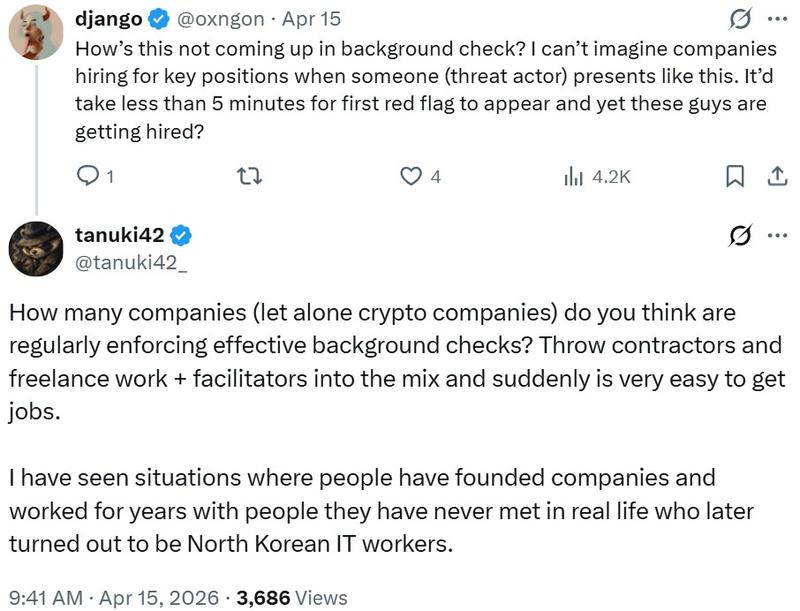
During March, the US Treasury Department imposed sanctions on six individuals and two entities for their purported involvement in North Korean IT worker fraud operations. Additionally, the FBI issued guidance in June, advising employers to authenticate candidates' professional backgrounds and mandate in-person meetings.
Nevertheless, the Drift exploit indicates Pyongyang's cyber operatives are evolving their tactics. The DeFi platform revealed its contributors were contacted in person by individuals presenting themselves as representatives of a quant trading firm at a prominent crypto conference in November. These attackers maintained communication and established trust before executing the breach.
Parallel to these major incidents, smaller-scale attacks have persisted. Crypto wallet provider Zerion reported that DPRK-affiliated actors employed AI-assisted social engineering techniques to steal approximately $100,000 in a distinct incident.
North Korea seldom addresses such allegations, although its foreign ministry released a statement in May 2020 rejecting involvement in cyberattacks and alleging that the United States was attempting to damage its reputation.
Retail crypto scams surge as DPRK tactics spill over
The Federal Bureau of Investigation (FBI) documented a 21% rise in cryptocurrency-related crime complaints in its 2025 Internet Crime Complaint Center (IC3) report. The FBI established IC3 in 2000 as a platform for victims within the US to report online fraud incidents.
Cryptocurrency cases accounted for 181,565 complaints in 2025, leading to $11.37 billion in losses, representing more than half of the total amount.
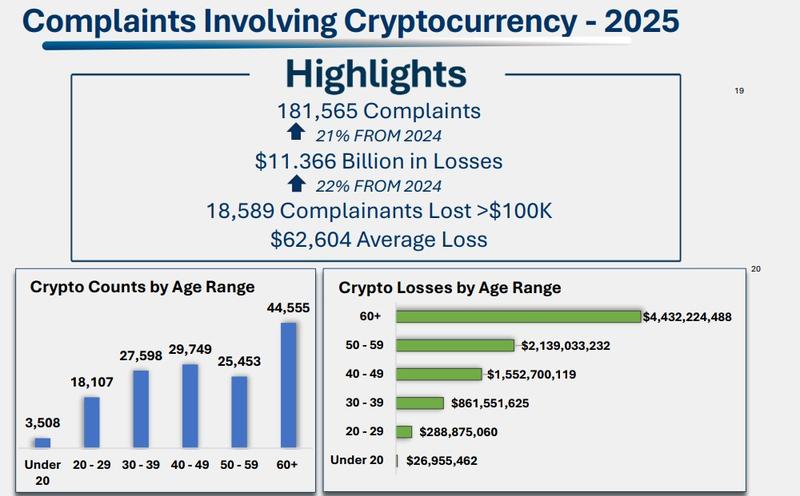
Americans aged 60 and above submitted the greatest number of cryptocurrency-related complaints. Investment scams constituted the largest category, producing 61,559 complaints, with 13,685 originating from individuals 60 and older.
However, this doesn't indicate the retail sector remains unaffected by suspected North Korean operations. An investigation released last November revealed that DPRK-affiliated operatives also enlist individuals to facilitate remote IT worker schemes.
During 2025, Heiner García, a cyberthreat intelligence expert at Telefónica, established contact with a suspected North Korean operative.
García previously informed Cointelegraph that the individual sought to use him as a proxy to circumvent VPN restrictions implemented by freelancing platforms. This tactic entails utilizing a victim's device in a local jurisdiction through the installation of remote access software such as AnyDesk.
In August 2024, the US Department of Justice apprehended Matthew Isaac Knoot for operating a "laptop farm" that enabled DPRK IT workers to present themselves as US-based employees using stolen identities. In July 2025, Christina Chapman received a sentence of more than eight years in prison for her participation in helping North Korean IT workers generate more than $17 million.
The tradeoff behind freezing funds stolen by suspected DPRK actors
A distinctive aspect of the Kelp DAO hack involved the Arbitrum Security Council's determination to freeze 30,766 ETH associated with the exploit.
Crypto's fundamental principle is decentralization, yet reactions to major hacks continue to create divisions within the industry. Some projects favor minimal intervention, even as security experts advocate for action, resulting in limited consensus regarding when intervention is appropriate.
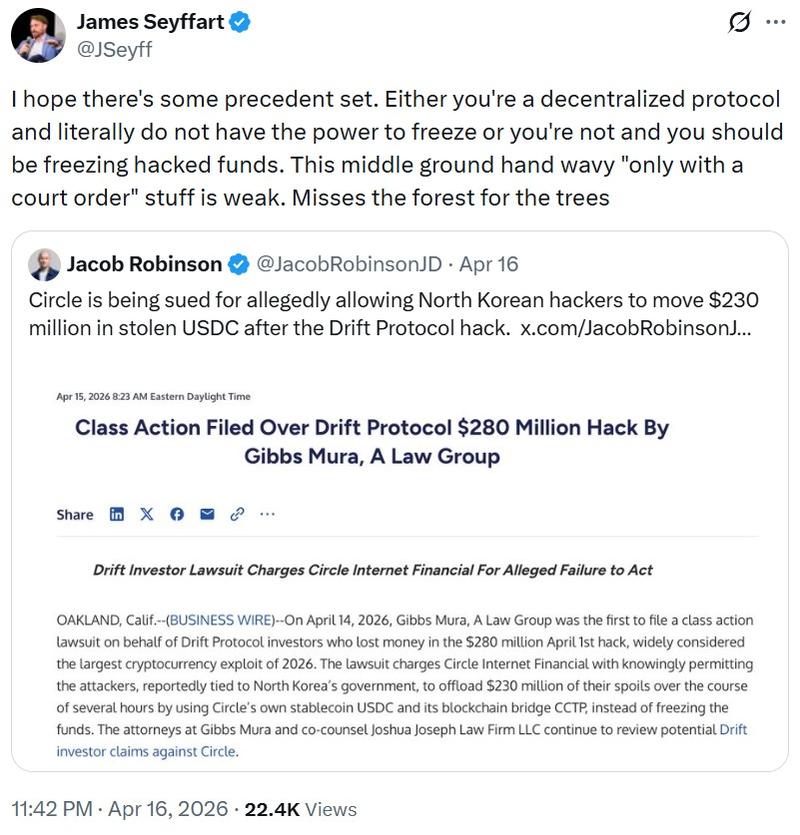
Ledger CTO Charles Guillemet stated on Tuesday that the outcome was "probably" good, but not a comfortable one. Freezing the funds likely averted additional losses. The discomfort arises from what the action makes explicit.
The Arbitrum Security Council did not leverage a bug or uncover a backdoor. It exercised its designated authority to override the state. This authority exists by design and creates tension with the concept of credibly neutral infrastructure. In practice, assets on today's rollups can still be influenced by governance decisions under specific conditions.
Guillemet connects that tradeoff to the threat environment. The Kelp DAO exploit did not depend on a novel smart contract bug. It revealed weaknesses in infrastructure and configuration, demonstrating how attacks are advancing beyond code into the systems that support it.
Simultaneously, North Korea-linked groups have developed into well-resourced, persistent adversaries with the capability to probe those systems across multiple fronts.
This leaves the industry divided between accepting intervention or accepting losses that cannot be reversed.