Security Researcher Reveals North Korean Tech Worker Ring Earning $1M Monthly
North Korean technology workers orchestrated cryptocurrency transactions via a server protected by the commonly used password "123456."

An operation involving North Korean technology workers generated over $3.5 million across several months by using fraudulent identities to secure positions as software developers while simultaneously targeting cryptocurrency platforms with hacking attempts, based on information obtained by a hacker who infiltrated one of their systems.
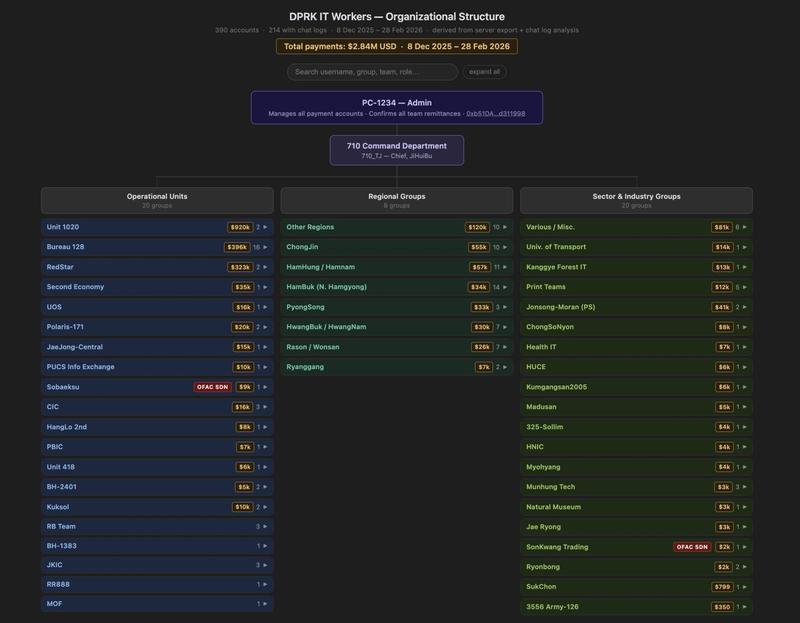
The compromised information acquired by the unidentified hacker was publicized by blockchain investigator ZachXBT through a Wednesday post on X. The data showed that a particular IT worker known as "Jerry," along with a network of 140 associates, were generating approximately $1 million each month, totaling $3.5 million in cryptocurrency since the end of November.
The technology workers from North Korea managed their payments through a website named "luckyguys.site" utilizing a collective password, "123456," according to ZachXBT, who noted that certain users on the platform seemed to be employed by Sobaeksu, Saenal and Songkwang, entities that have been sanctioned by the US Office of Foreign Assets Control.
The cryptocurrency payments they received were exchanged into traditional currency and transferred to banking accounts in China through digital payment services such as Payoneer. Investigation of these cryptocurrency wallet addresses additionally uncovered connections to other recognized North Korean wallets that were placed on Tether's blacklist in December, as ZachXBT explained.
Malicious actors originating from North Korea and various other nations persistently pose threats to the cryptocurrency sector through progressively advanced methods for executing hacks and fraudulent schemes.
Workers backed by the North Korean state have appropriated more than $7 billion in assets since 2009, with a substantial portion originating from cryptocurrency platforms. The $1.4 billion security breach of cryptocurrency exchange Bybit and the $625 million Ronin bridge compromise rank among its most significant operations.
Hackers from North Korea were additionally held responsible for the $280 million security breach of the Drift Protocol that occurred on April 1.
North Korean IT workers had a leaderboard
The North Korean technology workers whose information was leaked maintained a ranking system displaying the amount of cryptocurrency each worker had generated for the operation since Dec. 8, complete with references to blockchain explorer platforms containing transaction records.
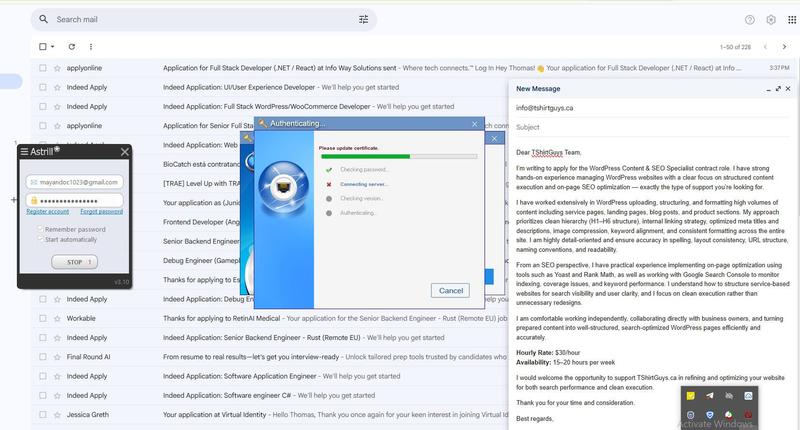
A separate screenshot published by ZachXBT demonstrated that Jerry utilized an Astrill virtual private network for accessing Gmail, through which he filed multiple applications for full-stack developer positions and software engineer opportunities on Indeed.
Within an email draft, Jerry composed a correspondence for a WordPress content and search engine optimization specialist role at a T-shirt business located in Texas, requesting $30 per hour with the capacity to work 15 to 20 hours weekly.
Identity documentation was fabricated as well, with one of the technology workers, identified as "Rascal," distributing images of a billing statement containing a fraudulent name and fabricated address in Hong Kong.
Rascal additionally distributed an image of an Irish passport, although it remains uncertain whether it was actually utilized.
ZachXBT nevertheless indicated these technology workers demonstrated less sophistication when compared to alternative North Korean collectives such as AppleJeus and TraderTraitor, which "operate far more efficiently and present the greatest risks to the industry."